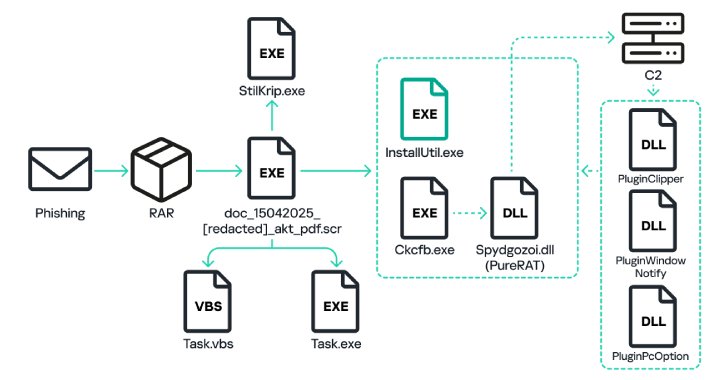
Russian organizations have become the target of a phishing campaign that distributes malware called PureRAT, according to new findings from Kaspersky.
“The campaign aimed at Russian business began back in March 2023, but in the first third of 2025 the number of attacks quadrupled compared to the same period in 2024,” the cybersecurity vendor said.
The attack chains, which have not been
Category: Data Breaches
Your blog category
-
PureRAT Malware Spikes 4x in 2025, Deploying PureLogs to Target Russian Firms
-
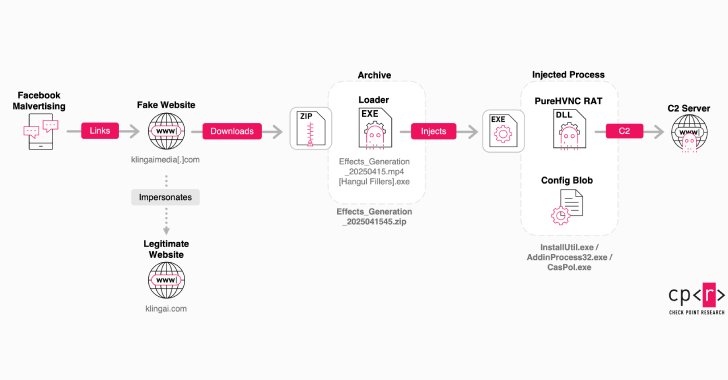
Fake Kling AI Facebook Ads Deliver RAT Malware to Over 22 Million Potential Victims
Counterfeit Facebook pages and sponsored ads on the social media platform are being employed to direct users to fake websites masquerading as Kling AI with the goal of tricking victims into downloading malware.
Kling AI is an artificial intelligence (AI)-powered platform to synthesize images and videos from text and image prompts. Launched in June 2024, it’s developed by Kuaishou Technology, -

Securing CI/CD workflows with Wazuh
Continuous Integration and Continuous Delivery/Deployment (CI/CD) refers to practices that automate how code is developed and released to different environments. CI/CD pipelines are fundamental in modern software development, ensuring code is consistently tested, built, and deployed quickly and efficiently.
While CI/CD automation accelerates software delivery, it can also introduce security -

How to Detect Phishing Attacks Faster: Tycoon2FA Example
It takes just one email to compromise an entire system. A single well-crafted message can bypass filters, trick employees, and give attackers the access they need. Left undetected, these threats can lead to credential theft, unauthorized access, and even full-scale breaches. As phishing techniques become more evasive, they can no longer be reliably caught by automated solutions alone.
Let’s take -
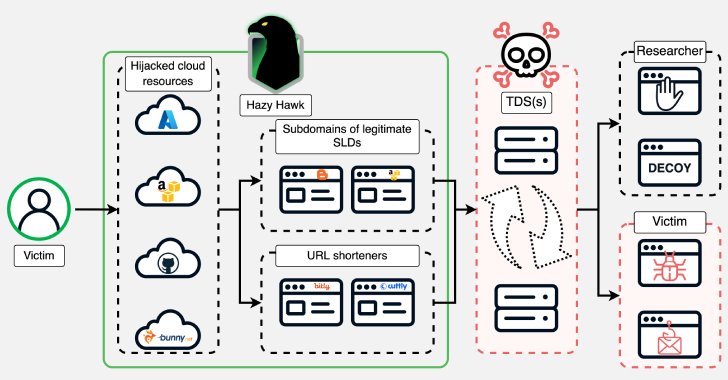
Hazy Hawk Exploits DNS Records to Hijack CDC, Corporate Domains for Malware Delivery
A threat actor known as Hazy Hawk has been observed hijacking abandoned cloud resources of high-profile organizations, including Amazon S3 buckets and Microsoft Azure endpoints, by leveraging misconfigurations in the Domain Name System (DNS) records.
The hijacked domains are then used to host URLs that direct users to scams and malware via traffic distribution systems (TDSes), according to -

100+ Fake Chrome Extensions Found Hijacking Sessions, Stealing Credentials, Injecting Ads
An unknown threat actor has been attributed to creating several malicious Chrome Browser extensions since February 2024 that masquerade as seemingly benign utilities but incorporate covert functionality to exfiltrate data, receive commands, and execute arbitrary code.
“The actor creates websites that masquerade as legitimate services, productivity tools, ad and media creation or analysis -

AWS Default IAM Roles Found to Enable Lateral Movement and Cross-Service Exploitation
Cybersecurity researchers have discovered risky default identity and access management (IAM) roles impacting Amazon Web Services that could open the door for attackers to escalate privileges, manipulate other AWS services, and, in some cases, even fully compromise AWS accounts.
“These roles, often created automatically or recommended during setup, grant overly broad permissions, such as full S3 -

The Crowded Battle: Key Insights from the 2025 State of Pentesting Report
In the newly released 2025 State of Pentesting Report, Pentera surveyed 500 CISOs from global enterprises (200 from within the USA) to understand the strategies, tactics, and tools they use to cope with the thousands of security alerts, the persisting breaches and the growing cyber risks they have to handle. The findings reveal a complex picture of progress, challenges, and a shifting mindset
-
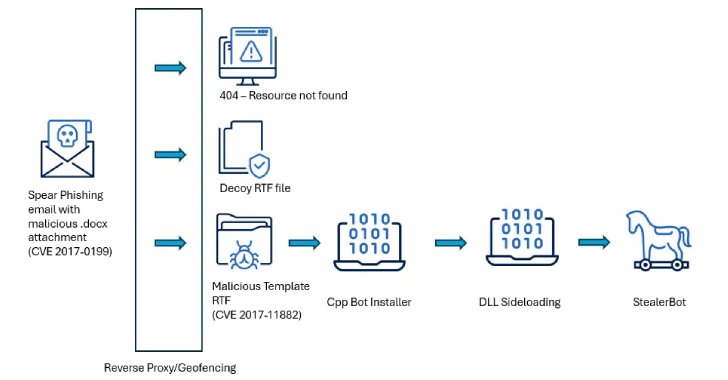
South Asian Ministries Hit by SideWinder APT Using Old Office Flaws and Custom Malware
High-level government institutions in Sri Lanka, Bangladesh, and Pakistan have emerged as the target of a new campaign orchestrated by a threat actor known as SideWinder.
“The attackers used spear phishing emails paired with geofenced payloads to ensure that only victims in specific countries received the malicious content,” Acronis researchers Santiago Pontiroli, Jozsef Gegeny, and Prakas -
RVTools Official Site Hacked to Deliver Bumblebee Malware via Trojanized Installer
The official site for RVTools has been hacked to serve a compromised installer for the popular VMware environment reporting utility.
“Robware.net and RVTools.com are currently offline. We are working expeditiously to restore service and appreciate your patience,” the company said in a statement posted on its website.
“Robware.net and RVTools.com are the only authorized and supported websites for