GitHub to Disable npm Install Scripts by Default to Stop Supply Chain Attacks
GitHub has announced what it said are “breaking changes” coming to npm version 12, one of which turns…
June 11, 2026
China-Linked JDY Botnet Expands to 1,500+ Devices for Cyber Reconnaissance
Cybersecurity researchers have warned of a “resurgence and expansion” of JDY, a covert network associated with China-nexus state-sponsored…
June 10, 2026
Ivanti, Fortinet, and SAP Release Patches for Multiple Critical Vulnerabilities
Fortinet, Ivanti, and SAP have released security updates to address multiple critical security vulnerabilities that could result in…
June 10, 2026
Unpatched Langflow Flaw CVE-2026-5027 Exploited for Unauthenticated RCE
A high-severity unpatched security flaw in Langflow, an open-source low-code platform to build artificial intelligence (AI) applications, has…
June 10, 2026
CISA Adds Cisco, Chrome, and Arista Flaws to KEV Catalog Amid Active Exploitation
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added three new vulnerabilities to its Known Exploited…
June 10, 2026
Anthropic Releases Claude Fable 5, Its Most Powerful AI Yet, With Cyber Safeguards
On June 9, Anthropic released Claude Fable 5, the most capable model it has ever made, generally available.…
June 10, 2026
ServiceNow Flaw Exploited to Gain Unauthorized Access to Customer Instances
ServiceNow has warned about a security incident in which unknown threat actors exploited a flaw to obtain deeper…
June 10, 2026
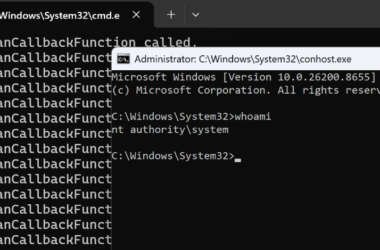
Microsoft Defender RoguePlanet Zero-Day Grants SYSTEM Access on Updated Windows
The anonymous security researcher going by the name Chaotic Eclipse (aka Nightmare-Eclipse) has released a proof-of-concept (PoC) exploit…
June 10, 2026
Six Proto6 Vulnerabilities in protobuf.js Expose Node.js Apps to RCE and DoS
Cybersecurity researchers have flagged half a dozen vulnerabilities in protobuf.js, a JavaScript and TypeScript implementation of Protocol Buffers…
June 10, 2026
Meta to Use Off-Site Business Data for Feed and AI Personalization
Meta on Tuesday announced that it will use information shared by other businesses to personalize users’ feed and…
June 9, 2026