Introduction
In recent years, conversational AI has advanced significantly, making it possible for people to communicate with computers more intuitively and naturally a more intuitive and natural way. OpenAI’s ChatGPT, an advanced messaging model, is one of the key innovations in this area. In this blog, we will explore the fascinating capabilities of ChatGPT, its impact on various industries, and the prospects of conversational AI.
Understanding ChatGPT
OpenAI created ChatGPT, an advanced language model. It is built upon the GPT-3.5 architecture and is designed to generate human-like responses based on given prompts or queries. The model has been trained on a vast amount of text data, enabling it to understand and generate coherent and contextually relevant responses.
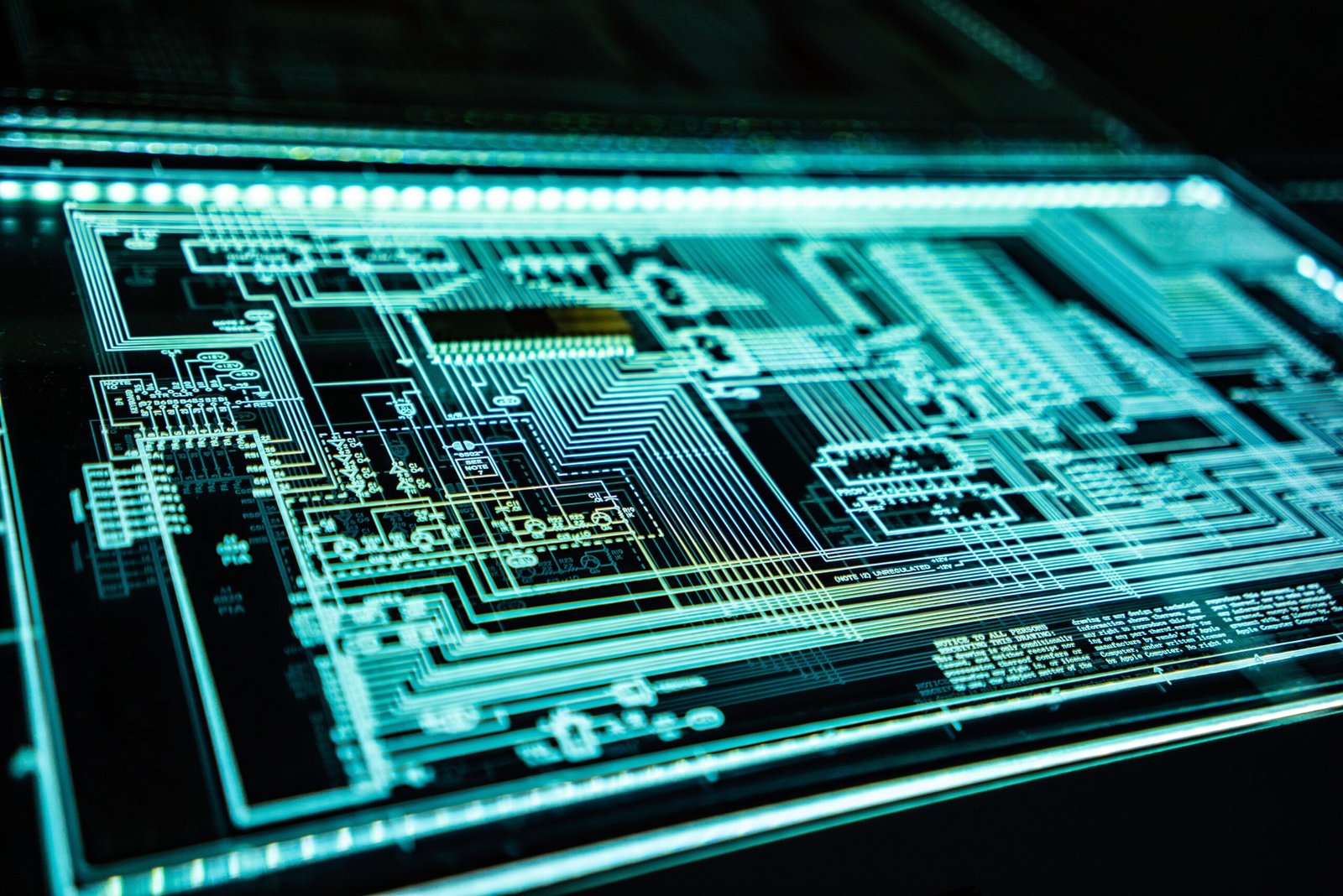
The Technology Behind ChatGPT
Deep learning algorithms and AI networks power ChatGPT. It utilizes a Transformer-based architecture that allows it to process and generate text in a highly efficient manner. The model leverages self-attention mechanisms to capture dependencies between words and generate meaningful responses.
Applications of ChatGPT
Customer Support
ChatGPT has revolutionized customer support by providing instant and personalized assistance. With its ability to understand natural language, ChatGPT can address customer queries, provide troubleshooting guidance, and offer product recommendations. This technology has significantly improved customer satisfaction and reduced the workload of human support agents.
Content Creation
ChatGPT has proven to be a valuable tool for content creators. It can assist in generating blog posts, articles, and social media content. By providing relevant information and creative suggestions, ChatGPT streamlines the content creation process and enhances productivity for writers.
Personal Assistants
In the form of virtual personal assistants, ChatGPT has become an indispensable tool for organizing tasks, managing schedules, and answering general inquiries. Its conversational abilities make it a versatile companion that can handle a wide range of daily tasks and provide useful recommendations.
Enhancing User Experience with ChatGPT
ChatGPT’s ability to enhance user experience stems from several key factors.
Natural Language Processing
ChatGPT excels in natural language processing, enabling it to understand and respond to human-like queries and prompts. Its comprehension of context and nuances enhances the overall conversational experience, making interactions with the model more intuitive and engaging.
Contextual Understanding
One of ChatGPT’s remarkable features is its ability to maintain context throughout a conversation. It can remember previous interactions and reference them appropriately, providing coherent and relevant responses. This contextual understanding contributes to a more natural and seamless user experience.
Personalization
ChatGPT can adapt its responses based on user preferences and individual writing styles. It can mimic the tone, style, and vocabulary of a specific user, creating a more personalized and engaging conversation. This feature makes ChatGPT a versatile tool for various professional and creative applications.
Limitations and Challenges
While ChatGPT offers impressive capabilities, it also faces certain limitations and challenges.
Bias and Ethical Concerns
Language models like ChatGPT may inadvertently learn biases present in the training data. This can lead to biased or inappropriate responses. Addressing these biases and ensuring the ethical use of the technology is an ongoing challenge that requires continuous improvement and scrutiny.
Privacy and Security
The vast amount of data processed by ChatGPT raises concerns about privacy and security. As conversational AI becomes more prevalent, it is crucial to implement robust security measures to protect user data and maintain confidentiality.
The Future of ChatGPT
ChatGPT has the potential to shape the future of conversational AI and human-computer interactions.
Advancements in AI Technology
As AI technology evolves, ChatGPT is expected to become even more powerful and capable. Future iterations may possess improved contextual understanding, better handling of complex queries, and enhanced creativity. Continued research and development will push the boundaries of conversational AI.
Ethical Guidelines and Regulations
To ensure the responsible and ethical use of conversational AI, it is essential to establish clear guidelines and regulations. This includes addressing biases, ensuring transparency, and safeguarding user privacy. Industry collaborations and ongoing discussions will shape the ethical framework for the future of AI.
Conclusion
ChatGPT, developed by OpenAI, has revolutionized conversational AI with its advanced language capabilities. Its applications span across industries, from customer support to content creation and personal assistance. By leveraging natural language processing and contextual understanding, ChatGPT enhances user experience and improves productivity. However, to optimize the technology, issues about opinions, privacy, and security must be resolved. As advancements continue and ethical guidelines evolve, ChatGPT will play a significant role in shaping the future of conversational AI.