Cybersecurity researchers have discovered a malicious package on the Python Package Index (PyPI) repository that purports to be an application related to the Solana blockchain, but contains malicious functionality to steal source code and developer secrets.
The package, named solana-token, is no longer available for download from PyPI, but not before it was downloaded 761 times. It was first
Category: Data Breaches
Your blog category
-

Malicious PyPI Package Posing as Solana Tool Stole Source Code in 761 Downloads
-
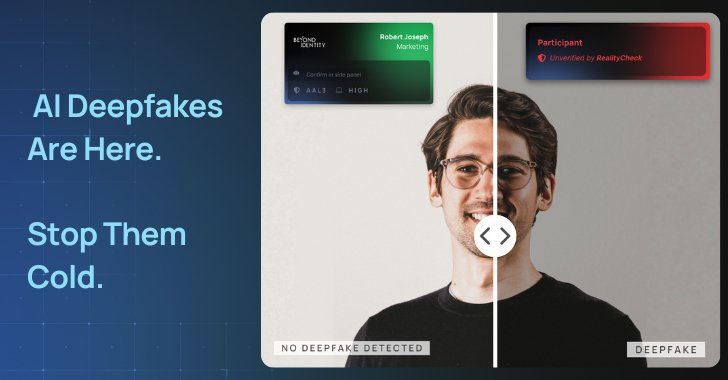
Deepfake Defense in the Age of AI
The cybersecurity landscape has been dramatically reshaped by the advent of generative AI. Attackers now leverage large language models (LLMs) to impersonate trusted individuals and automate these social engineering tactics at scale.
Let’s review the status of these rising attacks, what’s fueling them, and how to actually prevent, not detect, them.
The Most Powerful Person on the -

North Korean Konni APT Targets Ukraine with Malware to track Russian Invasion Progress
The North Korea-linked threat actor known as Konni APT has been attributed to a phishing campaign targeting government entities in Ukraine, indicating the threat actor’s targeting beyond Russia.
Enterprise security firm Proofpoint said the end goal of the campaign is to collect intelligence on the “trajectory of the Russian invasion.”
“The group’s interest in Ukraine follows historical targeting -

Moldovan Police Arrest Suspect in €4.5M Ransomware Attack on Dutch Research Agency
Moldovan law enforcement authorities have arrested a 45-year-old foreign man suspected of involvement in a series of ransomware attacks targeting Dutch companies in 2021.
“He is wanted internationally for committing several cybercrimes (ransomware attacks, blackmail, and money laundering) against companies based in the Netherlands,” officials said in a statement Monday.
In conjunction with the -
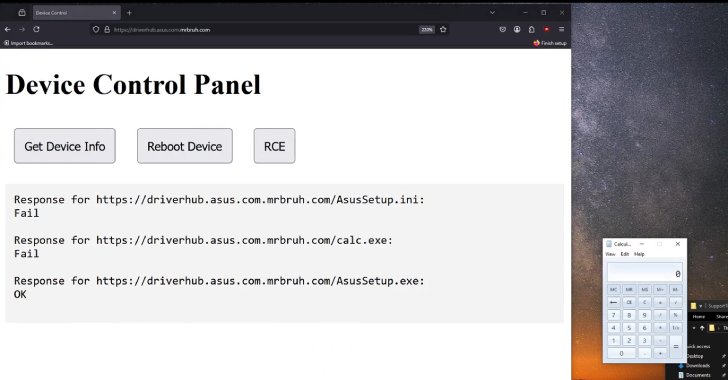
ASUS Patches DriverHub RCE Flaws Exploitable via HTTP and Crafted .ini Files
ASUS has released updates to address two security flaws impacting ASUS DriverHub that, if successfully exploited, could enable an attacker to leverage the software in order to achieve remote code execution.
DriverHub is a tool that’s designed to automatically detect the motherboard model of a computer and display necessary driver updates for subsequent installation by communicating with a -

⚡ Weekly Recap: Zero-Day Exploits, Developer Malware, IoT Botnets, and AI-Powered Scams
What do a source code editor, a smart billboard, and a web server have in common? They’ve all become launchpads for attacks—because cybercriminals are rethinking what counts as “infrastructure.” Instead of chasing high-value targets directly, threat actors are now quietly taking over the overlooked: outdated software, unpatched IoT devices, and open-source packages. It’s not just clever—it’s
-

The Persistence Problem: Why Exposed Credentials Remain Unfixed—and How to Change That
Detecting leaked credentials is only half the battle. The real challenge—and often the neglected half of the equation—is what happens after detection. New research from GitGuardian’s State of Secrets Sprawl 2025 report reveals a disturbing trend: the vast majority of exposed company secrets discovered in public repositories remain valid for years after detection, creating an expanding attack
-
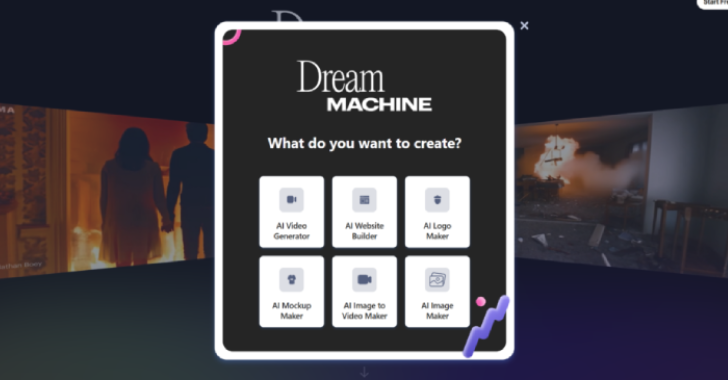
Fake AI Tools Used to Spread Noodlophile Malware, Targeting 62,000+ via Facebook Lures
Threat actors have been observed leveraging fake artificial intelligence (AI)-powered tools as a lure to entice users into downloading an information stealer malware dubbed Noodlophile.
“Instead of relying on traditional phishing or cracked software sites, they build convincing AI-themed platforms – often advertised via legitimate-looking Facebook groups and viral social media campaigns,” -
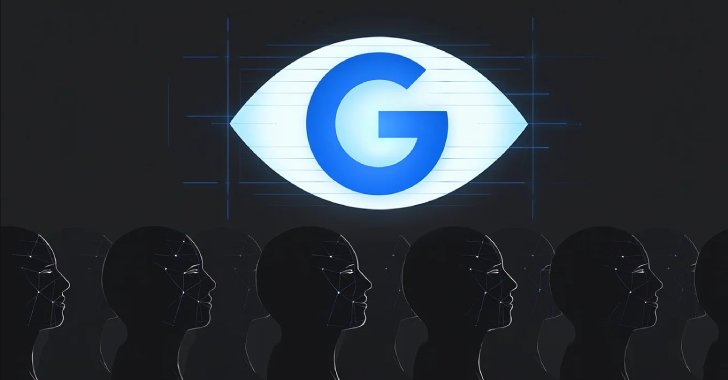
Google Pays $1.375 Billion to Texas Over Unauthorized Tracking and Biometric Data Collection
Google has agreed to pay the U.S. state of Texas nearly $1.4 billion to settle two lawsuits that accused the company of tracking users’ personal location and maintaining their facial recognition data without consent.
The $1.375 billion payment dwarfs the fines the tech giant has paid to settle similar lawsuits brought by other U.S. states. In November 2022, it paid $391 million to a group of 40 -

Germany Shuts Down eXch Over $1.9B Laundering, Seizes €34M in Crypto and 8TB of Data
Germany’s Federal Criminal Police Office (aka Bundeskriminalamt or BKA) has seized the online infrastructure and shutdown linked to the eXch cryptocurrency exchange over allegations of money laundering and operating a criminal trading platform.
The operation was carried out on April 30, 2025, authorities said, adding they also confiscated 8 terabytes worth of data and cryptocurrency assets