Cybersecurity researchers have discovered a malicious package on the Python Package Index (PyPI) repository that’s capable of harvesting sensitive developer-related information, such as credentials, configuration data, and environment variables, among others.
The package, named chimera-sandbox-extensions, attracted 143 downloads and likely targeted users of a service called Chimera Sandbox,
Category: Data Breaches
Your blog category
-

Malicious PyPI Package Masquerades as Chimera Module to Steal AWS, CI/CD, and macOS Data
-

Discord Invite Link Hijacking Delivers AsyncRAT and Skuld Stealer Targeting Crypto Wallets
A new malware campaign is exploiting a weakness in Discord’s invitation system to deliver an information stealer called Skuld and the AsyncRAT remote access trojan.
“Attackers hijacked the links through vanity link registration, allowing them to silently redirect users from trusted sources to malicious servers,” Check Point said in a technical report. “The attackers combined the ClickFix -
Over 269,000 Websites Infected with JSFireTruck JavaScript Malware in One Month
Cybersecurity researchers are calling attention to a “large-scale campaign” that has been observed compromising legitimate websites with malicious JavaScript injections.
According to Palo Alto Networks Unit 42, these malicious injects are obfuscated using JSFuck, which refers to an “esoteric and educational programming style” that uses only a limited set of characters to write and execute code. -

Ransomware Gangs Exploit Unpatched SimpleHelp Flaws to Target Victims with Double Extortion
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday disclosed that ransomware actors are targeting unpatched SimpleHelp Remote Monitoring and Management (RMM) instances to compromise customers of an unnamed utility billing software provider.
“This incident reflects a broader pattern of ransomware actors targeting organizations through unpatched versions of SimpleHelp -

CTEM is the New SOC: Shifting from Monitoring Alerts to Measuring Risk
Introduction: Security at a Tipping Point
Security Operations Centers (SOCs) were built for a different era, one defined by perimeter-based thinking, known threats, and manageable alert volumes. But today’s threat landscape doesn’t play by those rules. The sheer volume of telemetry, overlapping tools, and automated alerts has pushed traditional SOCs to the edge. Security teams are overwhelmed, -

Apple Zero-Click Flaw in Messages Exploited to Spy on Journalists Using Paragon Spyware
Apple has disclosed that a now-patched security flaw present in its Messages app was actively exploited in the wild to target civil society members in sophisticated cyber attacks.
The vulnerability, tracked as CVE-2025-43200, was addressed on February 10, 2025, as part of iOS 18.3.1, iPadOS 18.3.1, iPadOS 17.7.5, macOS Sequoia 15.3.1, macOS Sonoma 14.7.4, macOS Ventura 13.7.4, watchOS 11.3.1, -
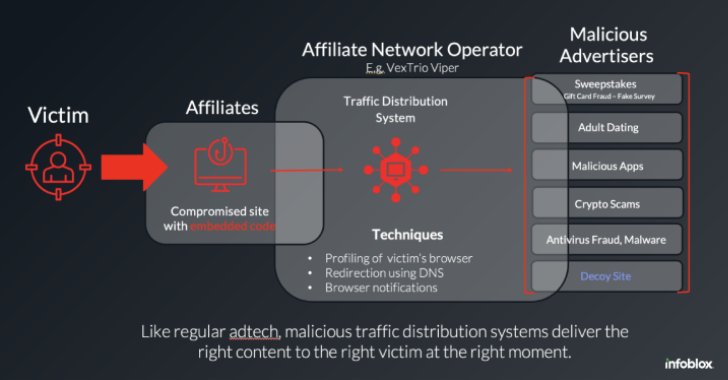
WordPress Sites Turned Weapon: How VexTrio and Affiliates Run a Global Scam Network
The threat actors behind the VexTrio Viper Traffic Distribution Service (TDS) have been linked to other TDS services like Help TDS and Disposable TDS, indicating that the sophisticated cybercriminal operation is a sprawling enterprise of its own that’s designed to distribute malicious content.
“VexTrio is a group of malicious adtech companies that distribute scams and harmful software via -
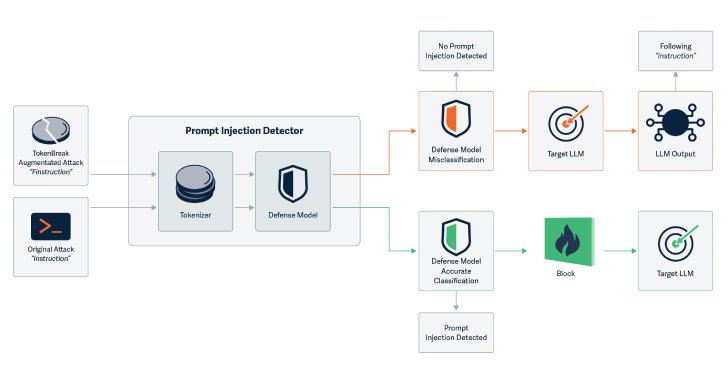
New TokenBreak Attack Bypasses AI Moderation with Single-Character Text Changes
Cybersecurity researchers have discovered a novel attack technique called TokenBreak that can be used to bypass a large language model’s (LLM) safety and content moderation guardrails with just a single character change.
“The TokenBreak attack targets a text classification model’s tokenization strategy to induce false negatives, leaving end targets vulnerable to attacks that the implemented -
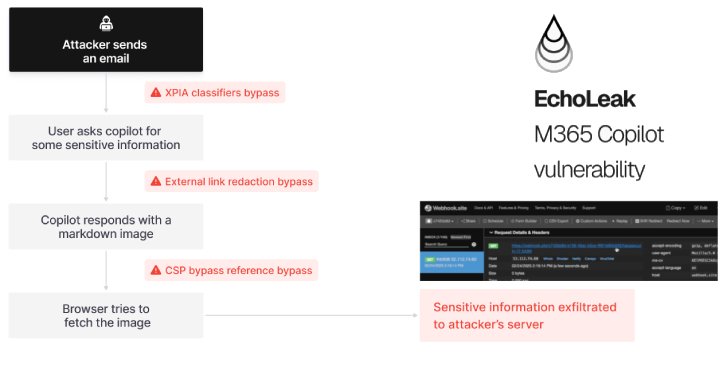
Zero-Click AI Vulnerability Exposes Microsoft 365 Copilot Data Without User Interaction
A novel attack technique named EchoLeak has been characterized as a “zero-click” artificial intelligence (AI) vulnerability that allows bad actors to exfiltrate sensitive data from Microsoft 365 Copilot’s context sans any user interaction.
The critical-rated vulnerability has been assigned the CVE identifier CVE-2025-32711 (CVSS score: 9.3). It requires no customer action and has been already -

Non-Human Identities: How to Address the Expanding Security Risk
Human identities management and control is pretty well done with its set of dedicated tools, frameworks, and best practices. This is a very different world when it comes to Non-human identities also referred to as machine identities. GitGuardian’s end-to-end NHI security platform is here to close the gap.
Enterprises are Losing Track of Their Machine Identities
Machine identities–service