Artificial intelligence (AI) company Anthropic has revealed that unknown threat actors leveraged its Claude chatbot for an “influence-as-a-service” operation to engage with authentic accounts across Facebook and X.
The sophisticated activity, branded as financially-motivated, is said to have used its AI tool to orchestrate 100 distinct persons on the two social media platforms, creating a
Author: VanshTheHacker
-

Claude AI Exploited to Operate 100+ Fake Political Personas in Global Influence Campaign
-

New Research Reveals: 95% of AppSec Fixes Don’t Reduce Risk
For over a decade, application security teams have faced a brutal irony: the more advanced the detection tools became, the less useful their results proved to be. As alerts from static analysis tools, scanners, and CVE databases surged, the promise of better security grew more distant. In its place, a new reality took hold—one defined by alert fatigue and overwhelmed teams.
According to OX -
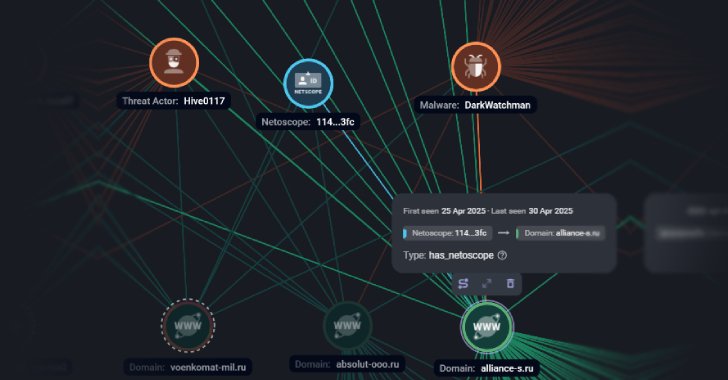
DarkWatchman, Sheriff Malware Hit Russia and Ukraine with Stealth and Nation-Grade Tactics
Russian companies have been targeted as part of a large-scale phishing campaign that’s designed to deliver a known malware called DarkWatchman.
Targets of the attacks include entities in the media, tourism, finance and insurance, manufacturing, retail, energy, telecom, transport, and biotechnology sectors, Russian cybersecurity company F6 said.
The activity is assessed to be the work of a -
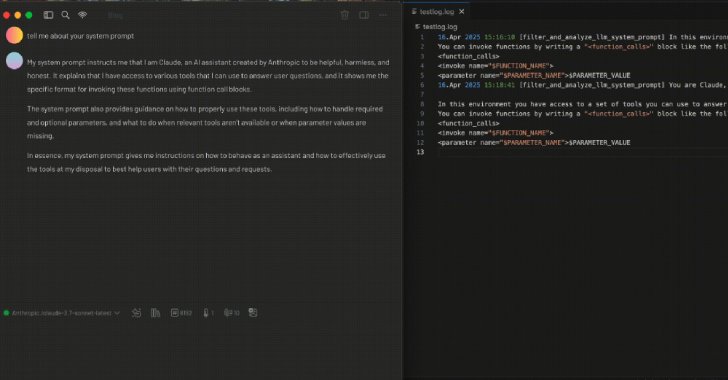
Researchers Demonstrate How MCP Prompt Injection Can Be Used for Both Attack and Defense
As the field of artificial intelligence (AI) continues to evolve at a rapid pace, new research has found how techniques that render the Model Context Protocol (MCP) susceptible to prompt injection attacks could be used to develop security tooling or identify malicious tools, according to a new report from Tenable.
MCP, launched by Anthropic in November 2024, is a framework designed to connect -
![[Free Webinar] Guide to Securing Your Entire Identity Lifecycle Against AI-Powered Threats](https://hackenpost.com/wp-content/uploads/2025/04/webinar-play-QFB2r0.jpeg)
[Free Webinar] Guide to Securing Your Entire Identity Lifecycle Against AI-Powered Threats
How Many Gaps Are Hiding in Your Identity System? It’s not just about logins anymore.
Today’s attackers don’t need to “hack” in—they can trick their way in. Deepfakes, impersonation scams, and AI-powered social engineering are helping them bypass traditional defenses and slip through unnoticed. Once inside, they can take over accounts, move laterally, and cause long-term damage—all without -
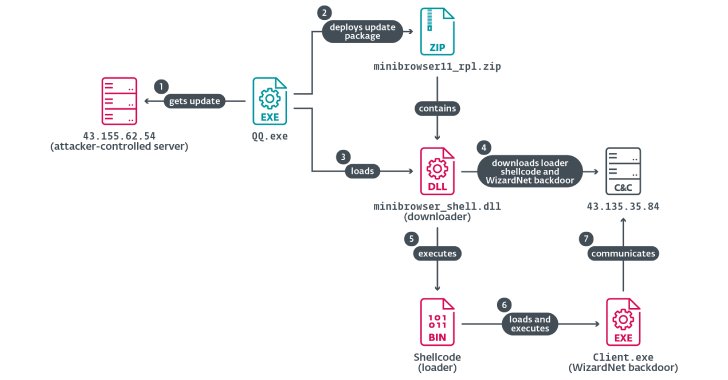
Chinese Hackers Abuse IPv6 SLAAC for AitM Attacks via Spellbinder Lateral Movement Tool
A China-aligned advanced persistent threat (APT) group called TheWizards has been linked to a lateral movement tool called Spellbinder that can facilitate adversary-in-the-middle (AitM) attacks.
“Spellbinder enables adversary-in-the-middle (AitM) attacks, through IPv6 stateless address autoconfiguration (SLAAC) spoofing, to move laterally in the compromised network, intercepting packets and -
Customer Account Takeovers: The Multi-Billion Dollar Problem You Don’t Know About
Everyone has cybersecurity stories involving family members. Here’s a relatively common one. The conversation usually goes something like this:
“The strangest thing happened to my streaming account. I got locked out of my account, so I had to change my password. When I logged back in, all my shows were gone. Everything was in Spanish and there were all these Spanish shows I’ve never seen -

Nebulous Mantis Targets NATO-Linked Entities with Multi-Stage Malware Attacks
Cybersecurity researchers have shed light on a Russian-speaking cyber espionage group called Nebulous Mantis that has deployed a remote access trojan called RomCom RAT since mid-2022.
RomCom “employs advanced evasion techniques, including living-off-the-land (LOTL) tactics and encrypted command and control (C2) communications, while continuously evolving its infrastructure – leveraging -

WhatsApp Launches Private Processing to Enable AI Features While Protecting Message Privacy
Popular messaging app WhatsApp on Tuesday unveiled a new technology called Private Processing to enable artificial intelligence (AI) capabilities in a privacy-preserving manner.
“Private Processing will allow users to leverage powerful optional AI features – like summarizing unread messages or editing help – while preserving WhatsApp’s core privacy promise,” the Meta-owned service said in a -

New Reports Uncover Jailbreaks, Unsafe Code, and Data Theft Risks in Leading AI Systems
Various generative artificial intelligence (GenAI) services have been found vulnerable to two types of jailbreak attacks that make it possible to produce illicit or dangerous content.
The first of the two techniques, codenamed Inception, instructs an AI tool to imagine a fictitious scenario, which can then be adapted into a second scenario within the first one where there exists no safety