Kimsuky Deploys HTTPSpy, Expands Arsenal with HelloDoor and VS Code Tunnels
The North Korean state-sponsored threat actor known as Kimsuky (aka Velvet Chollima) has been attributed to a fresh…
May 29, 2026
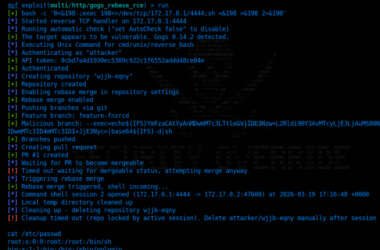
Critical Gogs RCE Vulnerability Lets Any Authenticated User Execute Arbitrary Code
A critical security vulnerability has been disclosed in Gogs, a popular open-source self-hosted Git service, that allows an…
May 28, 2026
Threat Actors Exploit Critical FortiClient EMS Flaw to Deploy Credential Stealer
Threat actors are continuing to exploit a critical, now-patched security flaw impacting FortiClient Endpoint Management Server (EMS) deployments…
May 28, 2026
Microsoft Slams Public Zero-Day Disclosures Amid GitHub Researcher Account Removal
Microsoft has come out strongly in favor of Coordinated Vulnerability Disclosure (CVD), urging the research community to share…
May 28, 2026
ThreatsDay Bulletin: Claude Security Plugin, Azure Priv-Esc, Kali365 MFA Bypass, FIFA Scams +15 More
Every time you think the industry has finally stopped doing some reckless, low-effort crap, somebody spins up a…
May 28, 2026
Grandoreiro Malware and BTMOB RAT Campaigns Target Windows and Android Users
Latin America and Europe become the target of two banking trojan campaigns that are designed to infect Windows…
May 27, 2026
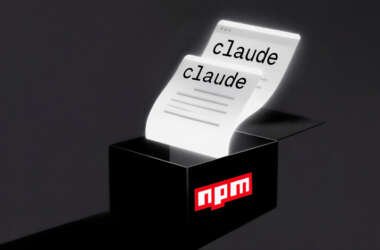
Malicious npm Package Stole Files From Claude AI User Directory via GitHub
Cybersecurity researchers have discovered a new malicious package on the npm registry that comes with information stealing capabilities.…
May 27, 2026
5 Steps to Managing Shadow AI Tools Without Slowing Down Employees
When an employee installs an AI writing assistant, connects a coding copilot to their IDE, or starts summarizing…
May 27, 2026
GlassWorm Malware Takedown Disrupts Developer Supply Chain Attack Infrastructure
CrowdStrike, in partnership with Google and the Shadowserver Foundation, has announced the simultaneous disruption of all command-and-control (C2)…
May 27, 2026
3 SOC Steps that Shut Down Incident Risks Early
Most organizations still picture cyber defense as a fortress problem: build stronger walls, add more guards, buy another…
May 27, 2026