Cyber threats are no longer coming from just malware or exploits. They’re showing up inside the tools, platforms, and ecosystems organizations use every day. As companies connect AI, cloud apps, developer tools, and communication systems, attackers are following those same paths.
A clear pattern this week: attackers are abusing trust. Trusted updates, trusted marketplaces, trusted apps, even
Author: VanshTheHacker
-
⚡ Weekly Recap: AI Skill Malware, 31Tbps DDoS, Notepad++ Hack, LLM Backdoors and More
-

How Top CISOs Solve Burnout and Speed up MTTR without Extra Hiring
Why do SOC teams keep burning out and missing SLAs even after spending big on security tools? Routine triage piles up, senior specialists get dragged into basic validation, and MTTR climbs, while stealthy threats still find room to slip through. Top CISOs have realized the solution isn’t hiring more people or stacking yet another tool onto the workflow, but giving their teams faster, clearer
-

OpenClaw Integrates VirusTotal Scanning to Detect Malicious ClawHub Skills
OpenClaw (formerly Moltbot and Clawdbot) has announced that it’s partnering with Google-owned VirusTotal to scan skills that are being uploaded to ClawHub, its skill marketplace, as part of broader efforts to bolster the security of the agentic ecosystem.
“All skills published to ClawHub are now scanned using VirusTotal’s threat intelligence, including their new Code Insight capability,” -

German Agencies Warn of Signal Phishing Targeting Politicians, Military, Journalists
Germany’s Federal Office for the Protection of the Constitution (aka Bundesamt für Verfassungsschutz or BfV) and Federal Office for Information Security (BSI) have issued a joint advisory warning of a malicious cyber campaign undertaken by a likely state-sponsored threat actor that involves carrying out phishing attacks over the Signal messaging app.
“The focus is on high-ranking targets in -
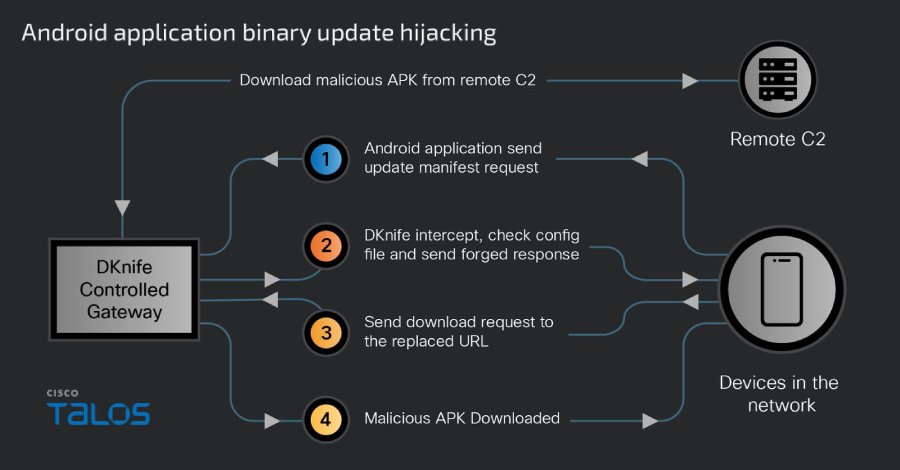
China-Linked DKnife AitM Framework Targets Routers for Traffic Hijacking, Malware Delivery
Cybersecurity researchers have taken the wraps off a gateway-monitoring and adversary-in-the-middle (AitM) framework dubbed DKnife that’s operated by China-nexus threat actors since at least 2019.
The framework comprises seven Linux-based implants that are designed to perform deep packet inspection, manipulate traffic, and deliver malware via routers and edge devices. Its primary targets seem to -

CISA Orders Removal of Unsupported Edge Devices to Reduce Federal Network Risk
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has ordered Federal Civilian Executive Branch (FCEB) agencies to strengthen asset lifecycle management for edge network devices and remove those that no longer receive security updates from original equipment manufacturers (OEMs) over the next 12 to 18 months.
The agency said the move is to drive down technical debt and minimize -

Asian State-Backed Group TGR-STA-1030 Breaches 70 Government, Infrastructure Entities
A previously undocumented cyber espionage group operating from Asia broke into the networks of at least 70 government and critical infrastructure organizations across 37 countries over the past year, according to new findings from Palo Alto Networks Unit 42.
In addition, the hacking crew has been observed conducting active reconnaissance against government infrastructure associated with 155 -
How Samsung Knox Helps Stop Your Network Security Breach
As you know, enterprise network security has undergone significant evolution over the past decade. Firewalls have become more intelligent, threat detection methods have advanced, and access controls are now more detailed. However (and it’s a big “however”), the increasing use of mobile devices in business operations necessitates network security measures that are specifically
-

New MongoDB Flaw Lets Unauthenticated Attackers Read Uninitialized Memory
A high-severity security flaw has been disclosed in MongoDB that could allow unauthenticated users to read uninitialized heap memory.
The vulnerability, tracked as CVE-2025-14847 (CVSS score: 8.7), has been described as a case of improper handling of length parameter inconsistency, which arises when a program fails to appropriately tackle scenarios where a length field is inconsistent with the -
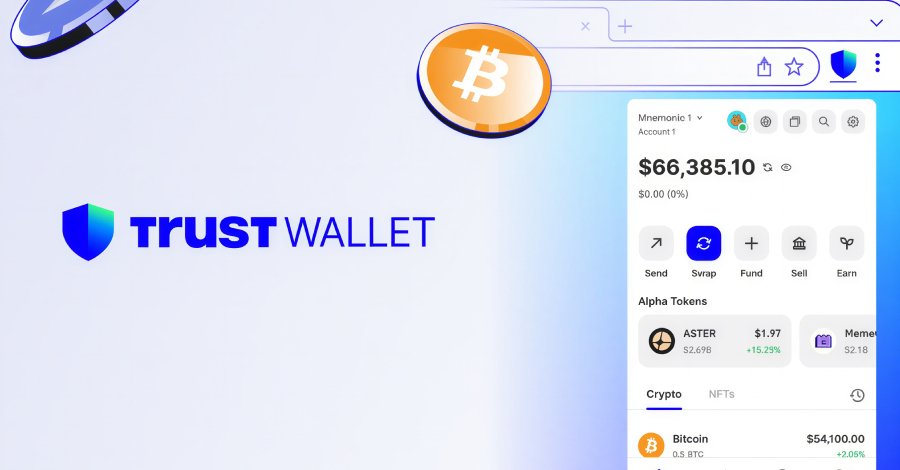
Trust Wallet Chrome Extension Breach Caused $7 Million Crypto Loss via Malicious Code
Trust Wallet is urging users to update its Google Chrome extension to the latest version following what it described as a “security incident” that led to the loss of approximately $7 million.
The issue, the multi‑chain, non‑custodial cryptocurrency wallet service said, impacts version 2.68. The extension has about one million users, according to the Chrome Web Store listing. Users are advised to