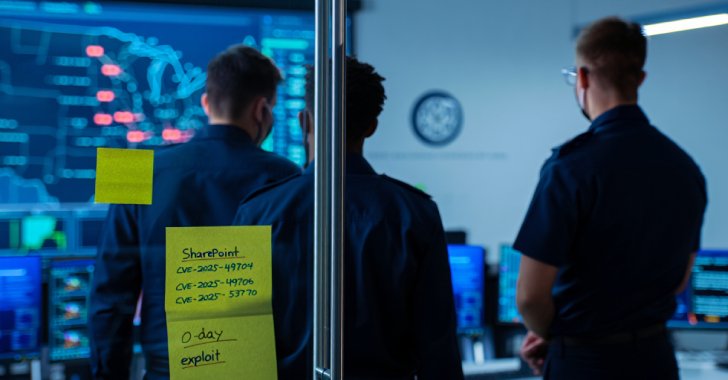
The U.S. Cybersecurity and Infrastructure Security Agency (CISA), on July 22, 2025, added two Microsoft SharePoint flaws, CVE-2025-49704 and CVE-2025-49706, to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation.
To that end, Federal Civilian Executive Branch (FCEB) agencies are required to remediate identified vulnerabilities by July 23, 2025.
“CISA is
Author: VanshTheHacker
-
CISA Orders Urgent Patching After Chinese Hackers Exploit SharePoint Flaws in Live Attacks
-

CISA Warns: SysAid Flaws Under Active Attack Enable Remote File Access and SSRF
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added two security flaws impacting SysAid IT support software to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation.
The vulnerabilities in question are listed below –CVE-2025-2775 (CVSS score: 9.3) – An improper restriction of XML external entity (XXE) reference vulnerability in the
-

Cisco Confirms Active Exploits Targeting ISE Flaws Enabling Unauthenticated Root Access
Cisco on Monday updated its advisory of a set of recently disclosed security flaws in Identity Services Engine (ISE) and ISE Passive Identity Connector (ISE-PIC) to acknowledge active exploitation.
“In July 2025, the Cisco PSIRT [Product Security Incident Response Team], became aware of attempted exploitation of some of these vulnerabilities in the wild,” the company said in an alert.
The -

Credential Theft and Remote Access Surge as AllaKore, PureRAT, and Hijack Loader Proliferate
Mexican organizations are still being targeted by threat actors to deliver a modified version of AllaKore RAT and SystemBC as part of a long-running campaign.
The activity has been attributed by Arctic Wolf Labs to a financially motivated hacking group called Greedy Sponge. It’s believed to be active since early 2021, indiscriminately targeting a wide range of sectors, such as retail, -

How to Advance from SOC Manager to CISO?
Making the move from managing a security operations center (SOC) to being a chief information security officer (CISO) is a significant career leap. Not only do you need a solid foundation of tech knowledge but also leadership skills and business smarts.
This article will guide you through the practical steps and skills you’ll need to nab an executive cybersecurity job and make the -

Hackers Exploit SharePoint Zero-Day Since July 7 to Steal Keys, Maintain Persistent Access
The recently disclosed critical Microsoft SharePoint vulnerability has been under exploitation as early as July 7, 2025, according to findings from Check Point Research.
The cybersecurity company said it observed first exploitation attempts targeting an unnamed major Western government, with the activity intensifying on July 18 and 19, spanning government, telecommunications, and software -

Iran-Linked DCHSpy Android Malware Masquerades as VPN Apps to Spy on Dissidents
Cybersecurity researchers have unearthed new Android spyware artifacts that are likely affiliated with the Iranian Ministry of Intelligence and Security (MOIS) and have been distributed to targets by masquerading as VPN apps and Starlink, a satellite internet connection service offered by SpaceX.
Mobile security vendor Lookout said it discovered four samples of a surveillanceware tool it tracks -

⚡ Weekly Recap: SharePoint 0-Day, Chrome Exploit, macOS Spyware, NVIDIA Toolkit RCE and More
Even in well-secured environments, attackers are getting in—not with flashy exploits, but by quietly taking advantage of weak settings, outdated encryption, and trusted tools left unprotected.
These attacks don’t depend on zero-days. They work by staying unnoticed—slipping through the cracks in what we monitor and what we assume is safe. What once looked suspicious now blends in, thanks to -
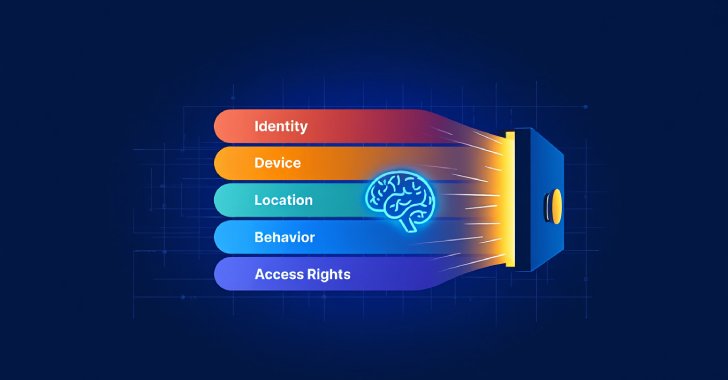
Assessing the Role of AI in Zero Trust
By 2025, Zero Trust has evolved from a conceptual framework into an essential pillar of modern security. No longer merely theoretical, it’s now a requirement that organizations must adopt. A robust, defensible architecture built on Zero Trust principles does more than satisfy baseline regulatory mandates. It underpins cyber resilience, secures third-party partnerships, and ensures uninterrupted
-

PoisonSeed Hackers Bypass FIDO Keys Using QR Phishing and Cross-Device Sign-In Abuse
Cybersecurity researchers have disclosed a novel attack technique that allows threat actors to downgrade Fast IDentity Online (FIDO) key protections by deceiving users into approving authentication requests from spoofed company login portals.FIDO keys are hardware- or software-based authenticators designed to eliminate phishing by binding logins to specific domains using public-private key