A China-linked threat actor known as Mustang Panda has been attributed to a new cyber espionage campaign directed against the Tibetan community.
The spear-phishing attacks leveraged topics related to Tibet, such as the 9th World Parliamentarians’ Convention on Tibet (WPCT), China’s education policy in the Tibet Autonomous Region (TAR), and a recently published book by the 14th Dalai Lama,
Author: VanshTheHacker
-

PUBLOAD and Pubshell Malware Used in Mustang Panda’s Tibet-Specific Attack
-

Business Case for Agentic AI SOC Analysts
Security operations centers (SOCs) are under pressure from both sides: threats are growing more complex and frequent, while security budgets are no longer keeping pace. Today’s security leaders are expected to reduce risk and deliver results without relying on larger teams or increased spending.
At the same time, SOC inefficiencies are draining resources. Studies show that up to half of all -

Chinese Group Silver Fox Uses Fake Websites to Deliver Sainbox RAT and Hidden Rootkit
A new campaign has been observed leveraging fake websites advertising popular software such as WPS Office, Sogou, and DeepSeek to deliver Sainbox RAT and the open-source Hidden rootkit.
The activity has been attributed with medium confidence to a Chinese hacking group called Silver Fox (aka Void Arachne), citing similarities in tradecraft with previous campaigns attributed to the threat actor. -

MOVEit Transfer Faces Increased Threats as Scanning Surges and CVE Flaws Are Targeted
Threat intelligence firm GreyNoise is warning of a “notable surge” in scanning activity targeting Progress MOVEit Transfer systems starting May 27, 2025—suggesting that attackers may be preparing for another mass exploitation campaign or probing for unpatched systems.MOVEit Transfer is a popular managed file transfer solution used by businesses and government agencies to share sensitive data
-
OneClik Malware Targets Energy Sector Using Microsoft ClickOnce and Golang Backdoors
Cybersecurity researchers have detailed a new campaign dubbed OneClik that leverages Microsoft’s ClickOnce software deployment technology and bespoke Golang backdoors to compromise organizations within the energy, oil, and gas sectors.
“The campaign exhibits characteristics aligned with Chinese-affiliated threat actors, though attribution remains cautious,” Trellix researchers Nico Paulo -

The Hidden Risks of SaaS: Why Built-In Protections Aren’t Enough for Modern Data Resilience
SaaS Adoption is Skyrocketing, Resilience Hasn’t Kept Pace
SaaS platforms have revolutionized how businesses operate. They simplify collaboration, accelerate deployment, and reduce the overhead of managing infrastructure. But with their rise comes a subtle, dangerous assumption: that the convenience of SaaS extends to resilience.
It doesn’t.
These platforms weren’t built with full-scale data -

Iranian APT35 Hackers Targeting Israeli Tech Experts with AI-Powered Phishing Attacks
An Iranian state-sponsored hacking group associated with the Islamic Revolutionary Guard Corps (IRGC) has been linked to a spear-phishing campaign targeting journalists, high-profile cyber security experts, and computer science professors in Israel.
“In some of those campaigns, Israeli technology and cyber security professionals were approached by attackers who posed as fictitious assistants to -
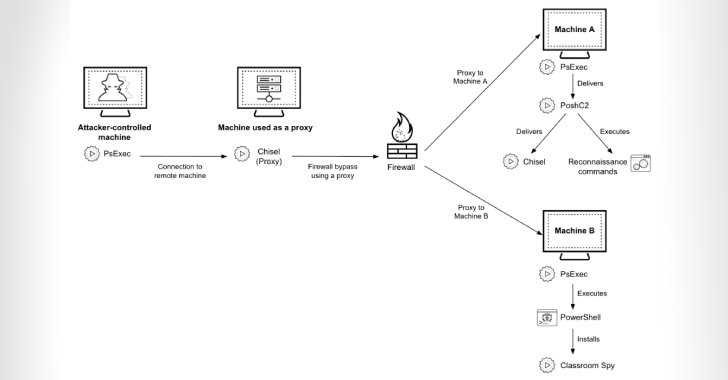
Cyber Criminals Exploit Open-Source Tools to Compromise Financial Institutions Across Africa
Cybersecurity researchers are calling attention to a series of cyber attacks targeting financial organizations across Africa since at least July 2023 using a mix of open-source and publicly available tools to maintain access.
Palo Alto Networks Unit 42 is tracking the activity under the moniker CL-CRI-1014, where “CL” refers to “cluster” and “CRI” stands for “criminal motivation.”
It’s suspected -

CISA Adds 3 Flaws to KEV Catalog, Impacting AMI MegaRAC, D-Link, Fortinet
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added three security flaws, each impacting AMI MegaRAC, D-Link DIR-859 router, and Fortinet FortiOS, to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation.
The list of vulnerabilities is as follows –CVE-2024-54085 (CVSS score: 10.0) – An authentication bypass by spoofing
-
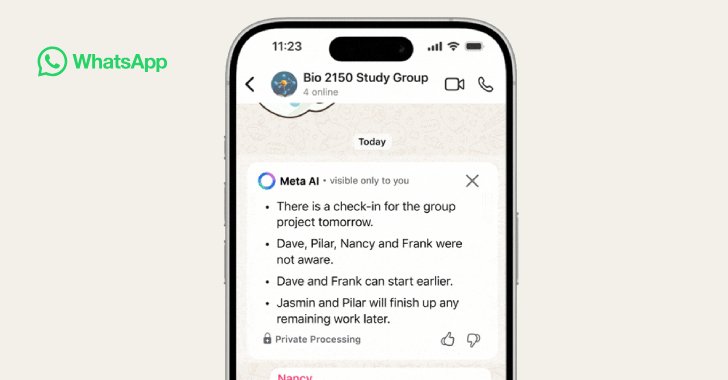
WhatsApp Adds AI-Powered Message Summaries for Faster Chat Previews
Popular messaging platform WhatsApp has added a new artificial intelligence (AI)-powered feature that leverages its in-house solution Meta AI to summarize unread messages in chats.
The feature, called Message Summaries, is currently rolling out in the English language to users in the United States, with plans to bring it to other regions and languages later this year.
It “uses Meta AI to