Samsung has released software updates to address a critical security flaw in MagicINFO 9 Server that has been actively exploited in the wild.
The vulnerability, tracked as CVE-2025-4632 (CVSS score: 9.8), has been described as a path traversal flaw.
“Improper limitation of a pathname to a restricted directory vulnerability in Samsung MagicINFO 9 Server version before 21.1052 allows attackers to
Author: VanshTheHacker
-

Samsung Patches CVE-2025-4632 Used to Deploy Mirai Botnet via MagicINFO 9 Exploit
-
BianLian and RansomExx Exploit SAP NetWeaver Flaw to Deploy PipeMagic Trojan
At least two different cybercrime groups BianLian and RansomExx are said to have exploited a recently disclosed security flaw in SAP NetWeaver, indicating that multiple threat actors are taking advantage of the bug.
Cybersecurity firm ReliaQuest, in a new update published today, said it uncovered evidence suggesting involvement from the BianLian data extortion crew and the RansomExx ransomware -

Xinbi Telegram Market Tied to $8.4B in Crypto Crime, Romance Scams, North Korea Laundering
A Chinese-language, Telegram-based marketplace called Xinbi Guarantee has facilitated no less than $8.4 billion in transactions since 2022, making it the second major black market to be exposed after HuiOne Guarantee.
According to a report published by blockchain analytics firm Elliptic, merchants on the marketplace have been found to peddle technology, personal data, and money laundering -

CTM360 Identifies Surge in Phishing Attacks Targeting Meta Business Users
A new global phishing threat called “Meta Mirage” has been uncovered, targeting businesses using Meta’s Business Suite. This campaign specifically aims at hijacking high-value accounts, including those managing advertising and official brand pages.
Cybersecurity researchers at CTM360 revealed that attackers behind Meta Mirage impersonate official Meta communications, tricking users into handing -

Earth Ammit Breached Drone Supply Chains via ERP in VENOM, TIDRONE Campaigns
A cyber espionage group known as Earth Ammit has been linked to two related but distinct campaigns from 2023 to 2024 targeting various entities in Taiwan and South Korea, including military, satellite, heavy industry, media, technology, software services, and healthcare sectors.
Cybersecurity firm Trend Micro said the first wave, codenamed VENOM, mainly targeted software service providers, while -

China-Linked APTs Exploit SAP CVE-2025-31324 to Breach 581 Critical Systems Worldwide
A recently disclosed critical security flaw impacting SAP NetWeaver is being exploited by multiple China-nexus nation-state actors to target critical infrastructure networks.
“Actors leveraged CVE-2025-31324, an unauthenticated file upload vulnerability that enables remote code execution (RCE),” EclecticIQ researcher Arda Büyükkaya said in an analysis published today.
Targets of the campaign -

Malicious PyPI Package Posing as Solana Tool Stole Source Code in 761 Downloads
Cybersecurity researchers have discovered a malicious package on the Python Package Index (PyPI) repository that purports to be an application related to the Solana blockchain, but contains malicious functionality to steal source code and developer secrets.
The package, named solana-token, is no longer available for download from PyPI, but not before it was downloaded 761 times. It was first -
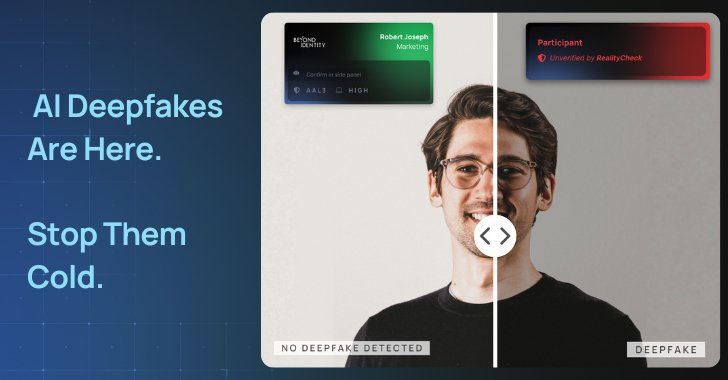
Deepfake Defense in the Age of AI
The cybersecurity landscape has been dramatically reshaped by the advent of generative AI. Attackers now leverage large language models (LLMs) to impersonate trusted individuals and automate these social engineering tactics at scale.
Let’s review the status of these rising attacks, what’s fueling them, and how to actually prevent, not detect, them.
The Most Powerful Person on the -

North Korean Konni APT Targets Ukraine with Malware to track Russian Invasion Progress
The North Korea-linked threat actor known as Konni APT has been attributed to a phishing campaign targeting government entities in Ukraine, indicating the threat actor’s targeting beyond Russia.
Enterprise security firm Proofpoint said the end goal of the campaign is to collect intelligence on the “trajectory of the Russian invasion.”
“The group’s interest in Ukraine follows historical targeting -

Moldovan Police Arrest Suspect in €4.5M Ransomware Attack on Dutch Research Agency
Moldovan law enforcement authorities have arrested a 45-year-old foreign man suspected of involvement in a series of ransomware attacks targeting Dutch companies in 2021.
“He is wanted internationally for committing several cybercrimes (ransomware attacks, blackmail, and money laundering) against companies based in the Netherlands,” officials said in a statement Monday.
In conjunction with the