Browsing Category
Data Breaches
1157 posts
Your blog category
INTERPOL Arrests 1,209 Cybercriminals Across 18 African Nations in Global Crackdown
INTERPOL on Friday announced that authorities from 18 countries across Africa have arrested 1,209 cybercriminals who targeted 88,000…
August 22, 2025
Ex-Developer Jailed Four Years for Sabotaging Ohio Employer with Kill-Switch Malware
A 55-year-old Chinese national has been sentenced to four years in prison and three years of supervised release…
August 22, 2025
Weak Passwords and Compromised Accounts: Key Findings from the Blue Report 2025
As security professionals, it’s easy to get caught up in a race to counter the latest advanced adversary…
August 21, 2025
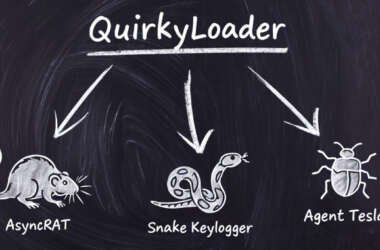
Hackers Using New QuirkyLoader Malware to Spread Agent Tesla, AsyncRAT and Snake Keylogger
Cybersecurity researchers have disclosed details of a new malware loader called QuirkyLoader that’s being used to deliver via…
August 21, 2025
Scattered Spider Hacker Gets 10 Years, $13M Restitution for SIM Swapping Crypto Theft
A 20-year-old member of the notorious cybercrime gang known as Scattered Spider has been sentenced to ten years…
August 21, 2025
Apple Patches CVE-2025-43300 Zero-Day in iOS, iPadOS, and macOS Exploited in Targeted Attacks
Apple has released security updates to address a security flaw impacting iOS, iPadOS, and macOS that it said…
August 21, 2025
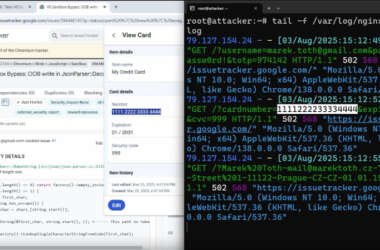
DOM-Based Extension Clickjacking Exposes Popular Password Managers to Credential and Data Theft
Popular password manager plugins for web browsers have been found susceptible to clickjacking security vulnerabilities that could be…
August 20, 2025
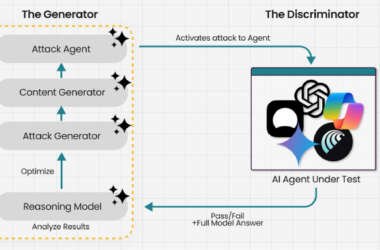
Experts Find AI Browsers Can Be Tricked by PromptFix Exploit to Run Malicious Hidden Prompts
Cybersecurity researchers have demonstrated a new prompt injection technique called PromptFix that tricks a generative artificial intelligence (GenAI)…
August 20, 2025
🕵️ Webinar: Discover and Control Shadow AI Agents in Your Enterprise Before Hackers Do
Do you know how many AI agents are running inside your business right now? If the answer is…
August 20, 2025
From Impact to Action: Turning BIA Insights Into Resilient Recovery
Modern businesses face a rapidly evolving and expanding threat landscape, but what does this mean for your business?…
August 20, 2025