Browsing Category
Data Breaches
1157 posts
Your blog category
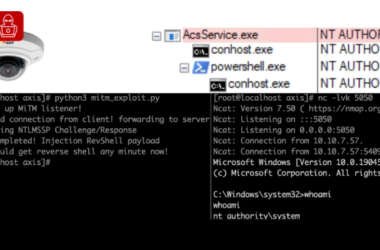
6,500 Axis Servers Expose Remoting Protocol, 4,000 in U.S. Vulnerable to Exploits
Cybersecurity researchers have disclosed multiple security flaws in video surveillance products from Axis Communications that, if successfully exploited,…
August 7, 2025
SonicWall Confirms Patched Vulnerability Behind Recent VPN Attacks, Not a Zero-Day
SonicWall has revealed that the recent spike in activity targeting its Gen 7 and newer firewalls with SSL…
August 7, 2025
AI Slashes Workloads for vCISOs by 68% as SMBs Demand More – New Report Reveals
As the volume and sophistication of cyber threats and risks grow, cybersecurity has become mission-critical for businesses of…
August 6, 2025
Microsoft Launches Project Ire to Autonomously Classify Malware Using AI Tools
Microsoft on Tuesday announced an autonomous artificial intelligence (AI) agent that can analyze and classify software without assistance…
August 6, 2025
Trend Micro Confirms Active Exploitation of Critical Apex One Flaws in On-Premise Systems
Trend Micro has released mitigations to address critical security flaws in on-premise versions of Apex One Management Console…
August 6, 2025
CERT-UA Warns of HTA-Delivered C# Malware Attacks Using Court Summons Lures
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of cyber attacks carried out by a threat…
August 6, 2025
AI Is Transforming Cybersecurity Adversarial Testing – Pentera Founder’s Vision
When Technology Resets the Playing Field In 2015 I founded a cybersecurity testing software company with the belief…
August 6, 2025
Google’s August Patch Fixes Two Qualcomm Vulnerabilities Exploited in the Wild
Google has released security updates to address multiple security flaws in Android, including fixes for two Qualcomm bugs…
August 5, 2025
Cursor AI Code Editor Vulnerability Enables RCE via Malicious MCP File Swaps Post Approval
Cybersecurity researchers have disclosed a high-severity security flaw in the artificial intelligence (AI)-powered code editor Cursor that could…
August 5, 2025
Misconfigurations Are Not Vulnerabilities: The Costly Confusion Behind Security Risks
In SaaS security conversations, “misconfiguration” and “vulnerability” are often used interchangeably. But they’re not the same thing. And…
August 5, 2025