Browsing Category
Data Breaches
1157 posts
Your blog category
New TETRA Radio Encryption Flaws Expose Law Enforcement Communications
Cybersecurity researchers have discovered a fresh set of security issues in the Terrestrial Trunked Radio (TETRA) communications protocol,…
August 11, 2025
Researchers Spot Surge in Erlang/OTP SSH RCE Exploits, 70% Target OT Firewalls
Malicious actors have been observed exploiting a now-patched critical security flaw impacting Erlang/Open Telecom Platform (OTP) SSH as…
August 11, 2025
⚡ Weekly Recap: BadCam Attack, WinRAR 0-Day, EDR Killer, NVIDIA Flaws, Ransomware Attacks & More
This week, cyber attackers are moving quickly, and businesses need to stay alert. They’re finding new weaknesses in…
August 11, 2025
6 Lessons Learned: Focusing Security Where Business Value Lives
The Evolution of Exposure Management Most security teams have a good sense of what’s critical in their environment.…
August 11, 2025
WinRAR Zero-Day Under Active Exploitation – Update to Latest Version Immediately
The maintainers of the WinRAR file archiving utility have released an update to address an actively exploited zero-day…
August 11, 2025
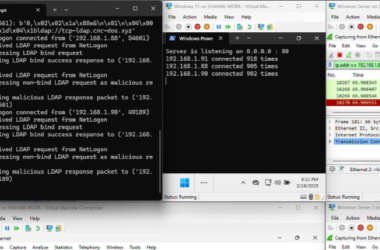
New Win-DDoS Flaws Let Attackers Turn Public Domain Controllers into DDoS Botnet via RPC, LDAP
A novel attack technique could be weaponized to rope thousands of public domain controllers (DCs) around the world…
August 10, 2025
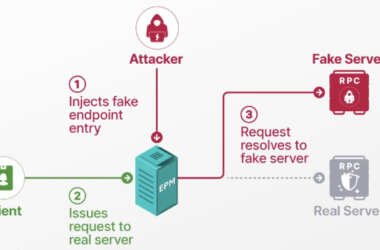
Researchers Detail Windows EPM Poisoning Exploit Chain Leading to Domain Privilege Escalation
Cybersecurity researchers have presented new findings related to a now-patched security issue in Microsoft’s Windows Remote Procedure Call…
August 10, 2025
Linux-Based Lenovo Webcams’ Flaw Can Be Remotely Exploited for BadUSB Attacks
Cybersecurity researchers have disclosed vulnerabilities in select model webcams from Lenovo that could turn them into BadUSB attack…
August 9, 2025
Researchers Reveal ReVault Attack Targeting Dell ControlVault3 Firmware in 100+ Laptop Models
Cybersecurity researchers have uncovered multiple security flaws in Dell’s ControlVault3 firmware and its associated Windows APIs that could…
August 9, 2025
Researchers Uncover GPT-5 Jailbreak and Zero-Click AI Agent Attacks Exposing Cloud and IoT Systems
Cybersecurity researchers have uncovered a jailbreak technique to bypass ethical guardrails erected by OpenAI in its latest large…
August 9, 2025