Wormable XMRig Campaign Uses BYOVD Exploit and Time-Based Logic Bomb
Cybersecurity researchers have disclosed details of a new cryptojacking campaign that uses pirated software bundles as lures to…
February 23, 2026
⚡ Weekly Recap: Double-Tap Skimmers, PromptSpy AI, 30Tbps DDoS, Docker Malware & More
Security news rarely moves in a straight line. This week, it feels more like a series of sharp…
February 23, 2026
How Exposed Endpoints Increase Risk Across LLM Infrastructure
As more organizations run their own Large Language Models (LLMs), they are also deploying more internal services and…
February 23, 2026
MuddyWater Targets MENA Organizations with GhostFetch, CHAR, and HTTP_VIP
The Iranian hacking group known as MuddyWater (aka Earth Vetala, Mango Sandstorm, and MUDDYCOAST) has targeted several organizations…
February 23, 2026
AI-Assisted Threat Actor Compromises 600+ FortiGate Devices in 55 Countries
A Russian-speaking, financially motivated threat actor has been observed taking advantage of commercial generative artificial intelligence (AI) services…
February 21, 2026
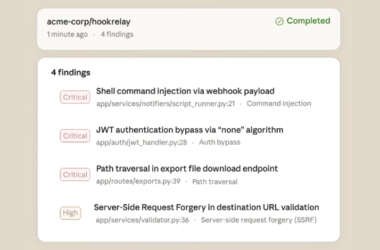
Anthropic Launches Claude Code Security for AI-Powered Vulnerability Scanning
Artificial intelligence (AI) company Anthropic has begun to roll out a new security feature for Claude Code that…
February 21, 2026
CISA Adds Two Actively Exploited Roundcube Flaws to KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added two security flaws impacting Roundcube webmail software…
February 21, 2026
EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
With $5.5 trillion in global AI risk exposure and 700,000 U.S. workers needing reskilling, four new AI certifications…
February 21, 2026
BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
Threat actors have been observed exploiting a recently disclosed critical security flaw impacting BeyondTrust Remote Support (RS) and…
February 20, 2026
Cline CLI 2.3.0 Supply Chain Attack Installed OpenClaw on Developer Systems
In yet another software supply chain attack, the open-source, artificial intelligence (AI)-powered coding assistant Cline CLI was updated…
February 20, 2026