When Your $2M Security Detection Fails: Can your SOC Save You?
Enterprises today are expected to have at least 6-8 detection tools, as detection is considered a standard investment…
November 26, 2025
Chrome Extension Caught Injecting Hidden Solana Transfer Fees Into Raydium Swaps
Cybersecurity researchers have discovered a new malicious extension on the Chrome Web Store that’s capable of injecting a…
November 26, 2025
Webinar: Learn to Spot Risks and Patch Safely with Community-Maintained Tools
If you’re using community tools like Chocolatey or Winget to keep systems updated, you’re not alone. These platforms…
November 26, 2025
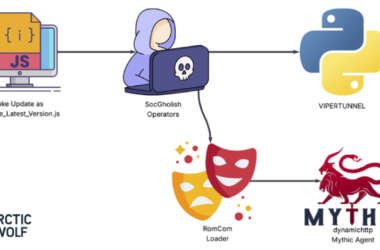
RomCom Uses SocGholish Fake Update Attacks to Deliver Mythic Agent Malware
The threat actors behind a malware family known as RomCom targeted a U.S.-based civil engineering company via a…
November 26, 2025
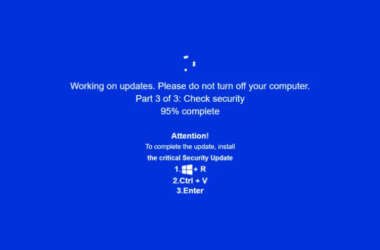
JackFix Uses Fake Windows Update Pop-Ups on Adult Sites to Deliver Multiple Stealers
Cybersecurity researchers are calling attention to a new campaign that’s leveraging a combination of ClickFix lures and fake…
November 25, 2025
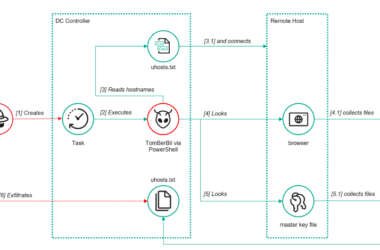
ToddyCat’s New Hacking Tools Steal Outlook Emails and Microsoft 365 Access Tokens
The threat actor known as ToddyCat has been observed adopting new methods to obtain access to corporate email…
November 25, 2025
3 SOC Challenges You Need to Solve Before 2026
2026 will mark a pivotal shift in cybersecurity. Threat actors are moving from experimenting with AI to making…
November 25, 2025
Hackers Hijack Blender 3D Assets to Deploy StealC V2 Data-Stealing Malware
Cybersecurity researchers have disclosed details of a new campaign that has leveraged Blender Foundation files to deliver an…
November 25, 2025
CISA Warns of Active Spyware Campaigns Hijacking High-Value Signal and WhatsApp Users
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday issued an alert warning of bad actors actively…
November 25, 2025
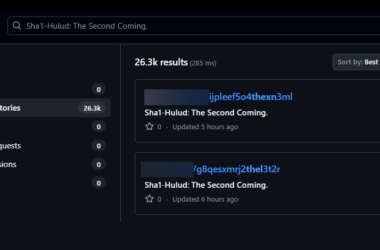
Second Sha1-Hulud Wave Affects 25,000+ Repositories via npm Preinstall Credential Theft
Multiple security vendors are sounding the alarm about a second wave of attacks targeting the npm registry in…
November 24, 2025