The Hidden Risks of SaaS: Why Built-In Protections Aren’t Enough for Modern Data Resilience
SaaS Adoption is Skyrocketing, Resilience Hasn’t Kept Pace SaaS platforms have revolutionized how businesses operate. They simplify collaboration,…
June 26, 2025
Iranian APT35 Hackers Targeting Israeli Tech Experts with AI-Powered Phishing Attacks
An Iranian state-sponsored hacking group associated with the Islamic Revolutionary Guard Corps (IRGC) has been linked to a…
June 26, 2025
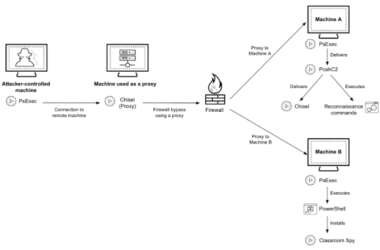
Cyber Criminals Exploit Open-Source Tools to Compromise Financial Institutions Across Africa
Cybersecurity researchers are calling attention to a series of cyber attacks targeting financial organizations across Africa since at…
June 26, 2025
CISA Adds 3 Flaws to KEV Catalog, Impacting AMI MegaRAC, D-Link, Fortinet
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added three security flaws, each impacting AMI MegaRAC,…
June 26, 2025
WhatsApp Adds AI-Powered Message Summaries for Faster Chat Previews
Popular messaging platform WhatsApp has added a new artificial intelligence (AI)-powered feature that leverages its in-house solution Meta…
June 26, 2025
Citrix Bleed 2 Flaw Enables Token Theft; SAP GUI Flaws Risk Sensitive Data Exposure
Cybersecurity researchers have detailed two now-patched security flaws in SAP Graphical User Interface (GUI) for Windows and Java…
June 25, 2025
Pro-Iranian Hacktivist Group Leaks Personal Records from the 2024 Saudi Games
Thousands of personal records allegedly linked to athletes and visitors of the Saudi Games have been published online…
June 25, 2025
Beware the Hidden Risk in Your Entra Environment
If you invite guest users into your Entra ID tenant, you may be opening yourself up to a…
June 25, 2025
SonicWall NetExtender Trojan and ConnectWise Exploits Used in Remote Access Attacks
Unknown threat actors have been distributing a trojanized version of SonicWall’s SSL VPN NetExtender application to steal credentials…
June 25, 2025
North Korea-linked Supply Chain Attack Targets Developers with 35 Malicious npm Packages
Cybersecurity researchers have uncovered a fresh batch of malicious npm packages linked to the ongoing Contagious Interview operation…
June 25, 2025