Researchers Detail Bitter APT’s Evolving Tactics as Its Geographic Scope Expands
The threat actor known as Bitter has been assessed to be a state-backed hacking group that’s tasked with…
June 5, 2025
Redefining Cyber Value: Why Business Impact Should Lead the Security Conversation
Security teams face growing demands with more tools, more data, and higher expectations than ever. Boards approve large…
June 5, 2025
Iran-Linked BladedFeline Hits Iraqi and Kurdish Targets with Whisper and Spearal Malware
An Iran-aligned hacking group has been attributed to a new set of cyber attacks targeting Kurdish and Iraqi…
June 5, 2025
DoJ Seizes 145 Domains Tied to BidenCash Carding Marketplace in Global Takedown
The U.S. Department of Justice (DoJ) on Wednesday announced the seizure of cryptocurrency funds and about 145 clearnet…
June 5, 2025
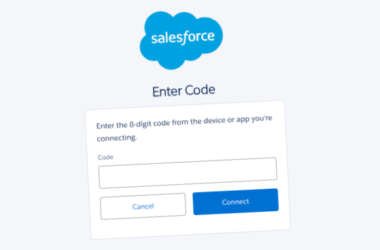
Google Exposes Vishing Group UNC6040 Targeting Salesforce with Fake Data Loader App
Google has disclosed details of a financially motivated threat cluster that it said “specialises” in voice phishing (aka…
June 4, 2025
Chaos RAT Malware Targets Windows and Linux via Fake Network Tool Downloads
Threat hunters are calling attention to a new variant of a remote access trojan (RAT) called Chaos RAT…
June 4, 2025
Your SaaS Data Isn’t Safe: Why Traditional DLP Solutions Fail in the Browser Era
Traditional data leakage prevention (DLP) tools aren’t keeping pace with the realities of how modern businesses use SaaS…
June 4, 2025
Malicious PyPI, npm, and Ruby Packages Exposed in Ongoing Open-Source Supply Chain Attacks
Several malicious packages have been uncovered across the npm, Python, and Ruby package repositories that drain funds from…
June 4, 2025
HPE Issues Security Patch for StoreOnce Bug Allowing Remote Authentication Bypass
Hewlett Packard Enterprise (HPE) has released security updates to address as many as eight vulnerabilities in its StoreOnce…
June 4, 2025
Fake DocuSign, Gitcode Sites Spread NetSupport RAT via Multi-Stage PowerShell Attack
Threat hunters are alerting to a new campaign that employs deceptive websites to trick unsuspecting users into executing…
June 3, 2025