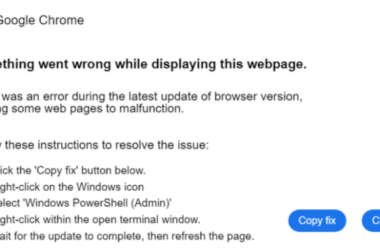
Hackers Use TikTok Videos to Distribute Vidar and StealC Malware via ClickFix Technique
The malware known as Latrodectus has become the latest to embrace the widely-used social engineering technique called ClickFix…
May 23, 2025
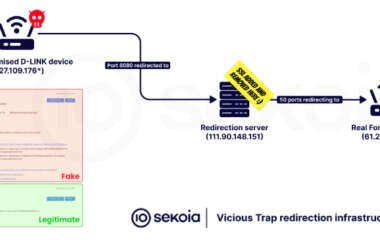
ViciousTrap Uses Cisco Flaw to Build Global Honeypot from 5,300 Compromised Devices
Cybersecurity researchers have disclosed that a threat actor codenamed ViciousTrap has compromised nearly 5,300 unique network edge devices…
May 23, 2025
300 Servers and €3.5M Seized as Europol Strikes Ransomware Networks Worldwide
As part of the latest “season” of Operation Endgame, a coalition of law enforcement agencies have taken down…
May 23, 2025
SafeLine WAF: Open Source Web Application Firewall with Zero-Day Detection and Bot Protection
From zero-day exploits to large-scale bot attacks — the demand for a powerful, self-hosted, and user-friendly web application…
May 23, 2025
U.S. Dismantles DanaBot Malware Network, Charges 16 in $50M Global Cybercrime Operation
The U.S. Department of Justice (DoJ) on Thursday announced the disruption of the online infrastructure associated with DanaBot…
May 23, 2025
Chinese Hackers Exploit Trimble Cityworks Flaw to Infiltrate U.S. Government Networks
A Chinese-speaking threat actor tracked as UAT-6382 has been linked to the exploitation of a now-patched remote-code-execution vulnerability…
May 22, 2025
Critical Windows Server 2025 dMSA Vulnerability Enables Active Directory Compromise
A privilege escalation flaw has been demonstrated in Windows Server 2025 that makes it possible for attackers to…
May 22, 2025
Chinese Hackers Exploit Ivanti EPMM Bugs in Global Enterprise Network Attacks
A recently patched pair of security flaws affecting Ivanti Endpoint Manager Mobile (EPMM) software has been exploited by…
May 22, 2025
Webinar: Learn How to Build a Reasonable and Legally Defensible Cybersecurity Program
It’s not enough to be secure. In today’s legal climate, you need to prove it. Whether you’re protecting…
May 22, 2025
Identity Security Has an Automation Problem—And It’s Bigger Than You Think
For many organizations, identity security appears to be under control. On paper, everything checks out. But new research…
May 22, 2025