Chinese Hackers Abuse IPv6 SLAAC for AitM Attacks via Spellbinder Lateral Movement Tool
A China-aligned advanced persistent threat (APT) group called TheWizards has been linked to a lateral movement tool called…
April 30, 2025
Customer Account Takeovers: The Multi-Billion Dollar Problem You Don’t Know About
Everyone has cybersecurity stories involving family members. Here’s a relatively common one. The conversation usually goes something like…
April 30, 2025
Nebulous Mantis Targets NATO-Linked Entities with Multi-Stage Malware Attacks
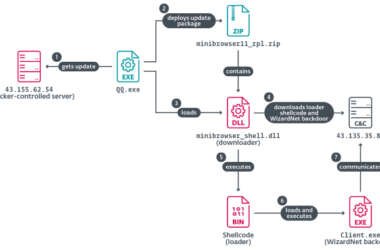
Cybersecurity researchers have shed light on a Russian-speaking cyber espionage group called Nebulous Mantis that has deployed a…
April 30, 2025
WhatsApp Launches Private Processing to Enable AI Features While Protecting Message Privacy
Popular messaging app WhatsApp on Tuesday unveiled a new technology called Private Processing to enable artificial intelligence (AI)…
April 29, 2025
New Reports Uncover Jailbreaks, Unsafe Code, and Data Theft Risks in Leading AI Systems
Various generative artificial intelligence (GenAI) services have been found vulnerable to two types of jailbreak attacks that make…
April 29, 2025
SentinelOne Uncovers Chinese Espionage Campaign Targeting Its Infrastructure and Clients
Cybersecurity company SentinelOne has revealed that a China-nexus threat cluster dubbed PurpleHaze conducted reconnaissance attempts against its infrastructure…
April 29, 2025
Product Walkthrough: Securing Microsoft Copilot with Reco
Find out how Reco keeps Microsoft 365 Copilot safe by spotting risky prompts, protecting data, managing user access,…
April 29, 2025
Google Reports 75 Zero-Days Exploited in 2024 — 44% Targeted Enterprise Security Products
Google has revealed that it observed 75 zero-day vulnerabilities exploited in the wild in 2024, down from 98…
April 29, 2025
⚡ Weekly Recap: Critical SAP Exploit, AI-Powered Phishing, Major Breaches, New CVEs & More
What happens when cybercriminals no longer need deep skills to breach your defenses? Today’s attackers are armed with…
April 28, 2025
How Breaches Start: Breaking Down 5 Real Vulns
Not every security vulnerability is high risk on its own – but in the hands of an advanced…
April 28, 2025