The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has sanctioned six individuals and two entities for their involvement in the Democratic People’s Republic of Korea (DPRK) information technology (IT) worker scheme with an aim to defraud U.S. businesses and generate illicit revenue for the regime to fund its weapons of mass destruction (WMD) programs.
“The North Korean
Author: VanshTheHacker
-

OFAC Sanctions DPRK IT Worker Network Funding WMD Programs Through Fake Remote Jobs
-
Interlock Ransomware Exploits Cisco FMC Zero-Day CVE-2026-20131 for Root Access
Amazon Threat Intelligence is warning of an active Interlock ransomware campaign that’s exploiting a recently disclosed critical security flaw in Cisco Secure Firewall Management Center (FMC) Software.
The vulnerability in question is CVE-2026-20131 (CVSS score: 10.0), a case of insecure deserialization of user-supplied Java byte stream, which could allow an unauthenticated, remote attacker to -

Product Walkthrough: How Mesh CSMA Reveals and Breaks Attack Paths to Crown Jewels
Security teams today are not short on tools or data. They are overwhelmed by both.
Yet within the terabytes of alerts, exposures, and misconfigurations – security teams still struggle to understand context:
Q: Which exposures, misconfigurations, and vulnerabilities chain together to create viable attack paths to crown jewels?
Even the most mature security teams can’t answer that -
Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit
A high-severity security flaw affecting default installations of Ubuntu Desktop versions 24.04 and later could be exploited to escalate privileges to the root level.
Tracked as CVE-2026-3888 (CVSS score: 7.8), the issue could allow an attacker to seize control of a susceptible system.
“This flaw (CVE-2026-3888) allows an unprivileged local attacker to escalate privileges to full root access -

Apple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS
Apple on Tuesday released its first round of Background Security Improvements to address a security flaw in WebKit that affects iOS, iPadOS, and macOS.
The vulnerability, tracked as CVE-2026-20643 (CVSS score: N/A), has been described as a cross-origin issue in WebKit’s Navigation API that could be exploited to bypass the same-origin policy when processing maliciously crafted web content.
The -
Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE via Port 23
Cybersecurity researchers have disclosed a critical security flaw impacting the GNU InetUtils telnet daemon (telnetd) that could be exploited by an unauthenticated remote attacker to execute arbitrary code with elevated privileges.
The vulnerability, tracked as CVE-2026-32746, carries a CVSS score of 9.8 out of 10.0. It has been described as a case of out-of-bounds write in the LINEMODE Set -

AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE
Cybersecurity researchers have disclosed details of a new method for exfiltrating sensitive data from artificial intelligence (AI) code execution environments using domain name system (DNS) queries.
In a report published Monday, BeyondTrust revealed that Amazon Bedrock AgentCore Code Interpreter’s sandbox mode permits outbound DNS queries that an attacker can exploit to enable interactive shells -
AI is Everywhere, But CISOs are Still Securing It with Yesterday’s Skills and Tools, Study Finds
A majority of security leaders are struggling to defend AI systems with tools and skills that are not fit for the challenge, according to the AI and Adversarial Testing Benchmark Report 2026 from Pentera.
The report, based on a survey of 300 US CISOs and senior security leaders, examines how organizations are securing AI infrastructure and highlights critical gaps tied to skills shortages and -
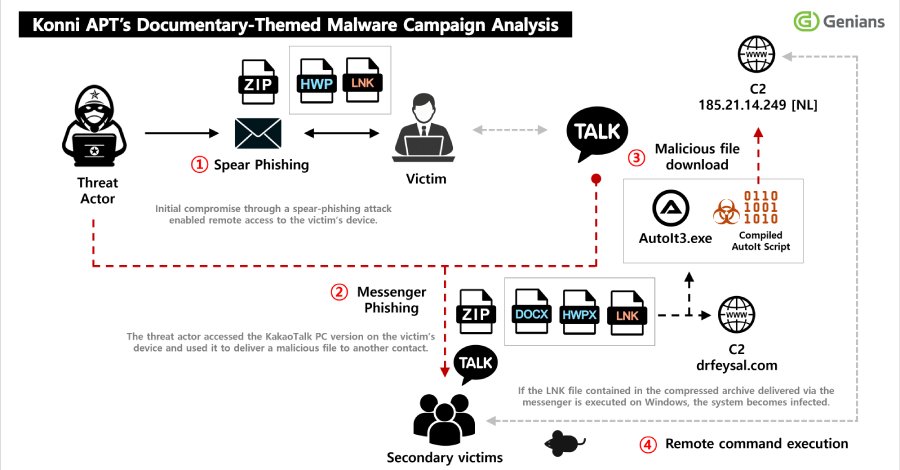
Konni Deploys EndRAT Through Phishing, Uses KakaoTalk to Propagate Malware
North Korean threat actors have been observed sending phishing to compromise targets and obtain access to a victim’s KakaoTalk desktop application to distribute malicious payloads to certain contacts.
The activity has been attributed by South Korean threat intelligence firm Genians to a hacking group referred to as Konni.
“Initial access was achieved through a spear-phishing email disguised as a -

CISA Flags Actively Exploited Wing FTP Vulnerability Leaking Server Paths
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Wing FTP to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation.
The vulnerability, CVE-2025-47813 (CVSS score: 4.3), is an information disclosure vulnerability that leaks the installation path of the application under certain conditions