On December 4, 2025, a 17-year-old was arrested in Osaka under Japan’s Unauthorized Access Prohibition Act. The young man had run malicious code to extract the personal data of over 7 million users of Kaikatsu Club, Japan’s largest internet cafe chain. When asked, the young man shared his motivation for the hack: he wanted to buy Pokémon cards.
In a sense, this is a fairly conventional story.
Author: VanshTheHacker
-

2026: The Year of AI-Assisted Attacks
-
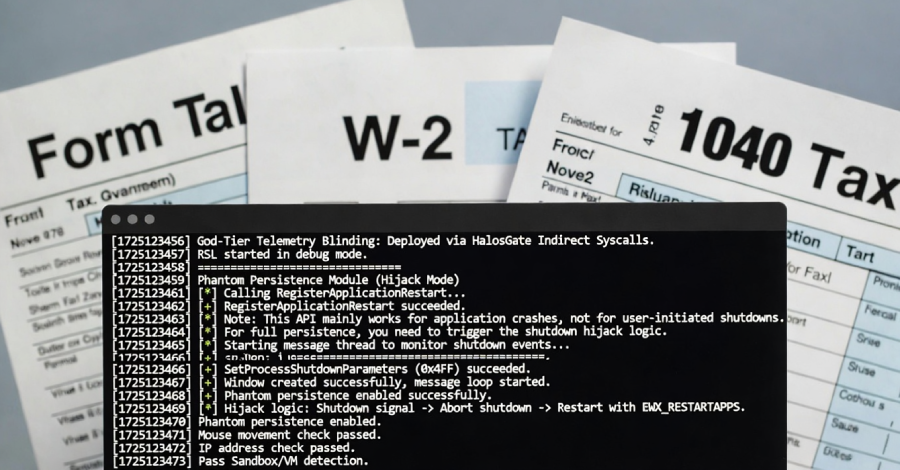
Silver Fox Deploys ABCDoor Malware via Tax-Themed Phishing in India and Russia
The China-based cybercrime group known as Silver Fox has been linked to a new campaign targeting organizations in Russia and India with a new malware called ABCDoor.
The activity involved using phishing emails that mimic correspondence from the Income Tax Department of India in December 2025, followed by a similar campaign aimed at Russian entities.
“Both waves followed a nearly identical -

Critical cPanel Vulnerability Weaponized to Target Government and MSP Networks
A previously unknown threat actor has been observed targeting government and military entities in Southeast Asia, alongside a smaller cluster of managed service providers (MSPs) and hosting providers in the Philippines, Laos, Canada, South Africa, and the U.S., by exploiting the recently disclosed vulnerability in cPanel.
The activity, detected by Ctrl-Alt-Intel on May 2, 2026, involves the -
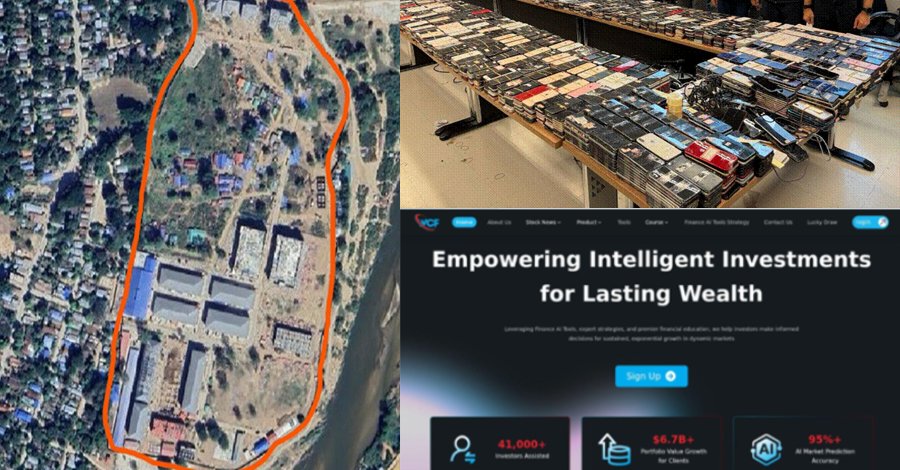
Global Crackdown Arrests 276, Shuts 9 Crypto Scam Centers, Seizes $701M
A coordinated international operation involving U.S. and Chinese authorities has arrested at least 276 suspects and shut down nine scam centers used for cryptocurrency investment fraud schemes targeting Americans, resulting in millions of dollars in losses.
The crackdown was led by the Dubai Police, under the United Arab Emirates (UAE) Ministry of Interior, in partnership with the U.S. Federal -
CISA Adds Actively Exploited Linux Root Access Bug CVE-2026-31431 to KEV
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a recently disclosed security flaw impacting various Linux distributions to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild.
The vulnerability, tracked as CVE-2026-31431 (CVSS score: 7.8), is a case of local privilege escalation (LPE) flaw that could allow an -

Trellix Confirms Source Code Breach With Unauthorized Repository Access
Cybersecurity company Trellix has announced that it suffered a breach that enabled unauthorized access to a “portion” of its source code.
It said it “recently identified” the compromise of its source code repository and that it began working with “leading forensic experts” to resolve the matter immediately. It also said it has notified law enforcement of the matter.
Trellix did not disclose the -
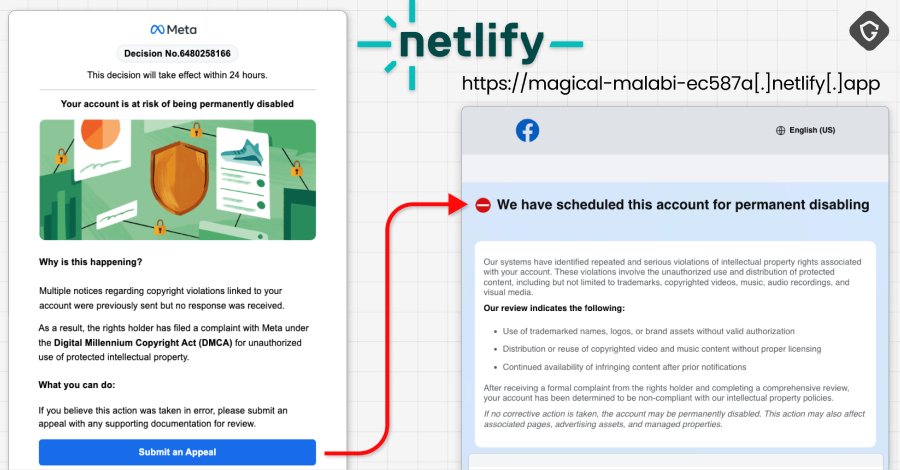
30,000 Facebook Accounts Hacked via Google AppSheet Phishing Campaign
A newly discovered Vietnamese-linked operation has been observed using a Google AppSheet as a “phishing relay” to distribute phishing emails with an aim to compromise Facebook accounts.
The activity has been codenamed AccountDumpling by Guardio, with the scheme selling the stolen accounts back through an illicit storefront run by the threat actors. In all, roughly 30,000 Facebook accounts are -
Cybercrime Groups Using Vishing and SSO Abuse in Rapid SaaS Extortion Attacks
Cybersecurity researchers are warning of two cybercrime groups that are carrying out “rapid, high-impact attacks” operating almost within the confines of SaaS environments, while leaving minimal traces of their actions.
The clusters, Cordial Spider (aka BlackFile, CL-CRI-1116, O-UNC-045, and UNC6671) and Snarky Spider (aka O-UNC-025 and UNC6661), have been attributed to high-speed data theft and -

China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists
Cybersecurity researchers have disclosed details of a new China-aligned espionage campaign targeting government and defense sectors across South, East, and Southeast Asia, along with one European government belonging to NATO.
Trend Micro has attributed the activity to a threat activity cluster it tracks under the temporary designation SHADOW-EARTH-053. The adversarial collective is assessed to -

Top Five Sales Challenges Costing MSPs Cybersecurity Revenue
The managed security services market is projected to grow from $38.31 billion in 2025 to $69.16 billion by 2030[1], with cybersecurity being the fastest-growing sector[2]. Despite this opportunity, many MSPs leave revenue on the table because their go-to-market strategy fails to connect technical expertise with business needs.
This execution gap is where most deals stall. MSPs often focus on