Federal prosecutors in the U.S. have accused a trio of allegedly hacking the networks of five U.S. companies with BlackCat (aka ALPHV) ransomware between May and November 2023 and extorting them.
Ryan Clifford Goldberg, Kevin Tyler Martin, and an unnamed co–conspirator (aka “Co-Conspirator 1”) based in Florida, all U.S. nationals, are said to have used the ransomware strain against a medical
Author: VanshTheHacker
-

U.S. Prosecutors Indict Cybersecurity Insiders Accused of BlackCat Ransomware Attacks
-
Microsoft Detects “SesameOp” Backdoor Using OpenAI’s API as a Stealth Command Channel
Microsoft has disclosed details of a novel backdoor dubbed SesameOp that uses OpenAI Assistants Application Programming Interface (API) for command-and-control (C2) communications.
“Instead of relying on more traditional methods, the threat actor behind this backdoor abuses OpenAI as a C2 channel as a way to stealthily communicate and orchestrate malicious activities within the compromised -

⚡ Weekly Recap: Lazarus Hits Web3, Intel/AMD TEEs Cracked, Dark Web Leak Tool & More
Cyberattacks are getting smarter and harder to stop. This week, hackers used sneaky tools, tricked trusted systems, and quickly took advantage of new security problems—some just hours after being found. No system was fully safe.
From spying and fake job scams to strong ransomware and tricky phishing, the attacks came from all sides. Even encrypted backups and secure areas were put to the test. -

The Evolution of SOC Operations: How Continuous Exposure Management Transforms Security Operations
Security Operations Centers (SOC) today are overwhelmed. Analysts handle thousands of alerts every day, spending much time chasing false positives and adjusting detection rules reactively. SOCs often lack the environmental context and relevant threat intelligence needed to quickly verify which alerts are truly malicious. As a result, analysts spend excessive time manually triaging alerts, the
-

Researchers Uncover BankBot-YNRK and DeliveryRAT Android Trojans Stealing Financial Data
Cybersecurity researchers have shed light on two different Android trojans called BankBot-YNRK and DeliveryRAT that are capable of harvesting sensitive data from compromised devices.
According to CYFIRMA, which analyzed three different samples of BankBot-YNRK, the malware incorporates features to sidestep analysis efforts by first checking its running within a virtualized or emulated environment -
New HttpTroy Backdoor Poses as VPN Invoice in Targeted Cyberattack on South Korea
The North Korea-linked threat actor known as Kimsuky has distributed a previously undocumented backdoor codenamed HttpTroy as part of a likely spear-phishing attack targeting a single victim in South Korea.
Gen Digital, which disclosed details of the activity, did not reveal any details on when the incident occurred, but noted that the phishing email contained a ZIP file (“250908_A_HK이노션 -

ASD Warns of Ongoing BADCANDY Attacks Exploiting Cisco IOS XE Vulnerability
The Australian Signals Directorate (ASD) has issued a bulletin about ongoing cyber attacks targeting unpatched Cisco IOS XE devices in the country with a previously undocumented implant known as BADCANDY.
The activity, per the intelligence agency, involves the exploitation of CVE-2023-20198 (CVSS score: 10.0), a critical vulnerability that allows a remote, unauthenticated attacker to create an -
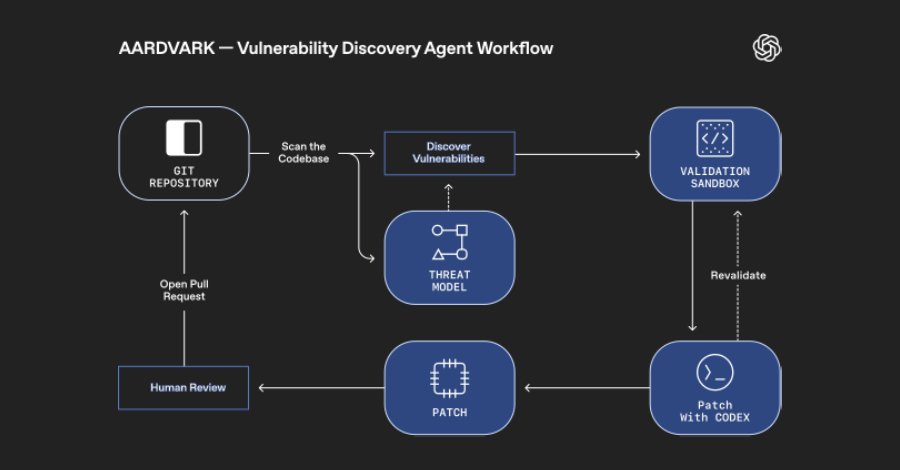
OpenAI Unveils Aardvark: GPT-5 Agent That Finds and Fixes Code Flaws Automatically
OpenAI has announced the launch of an “agentic security researcher” that’s powered by its GPT-5 large language model (LLM) and is programmed to emulate a human expert capable of scanning, understanding, and patching code.
Called Aardvark, the artificial intelligence (AI) company said the autonomous agent is designed to help developers and security teams flag and fix security vulnerabilities at -

Nation-State Hackers Deploy New Airstalk Malware in Suspected Supply Chain Attack
A suspected nation-state threat actor has been linked to the distribution of a new malware called Airstalk as part of a likely supply chain attack.
Palo Alto Networks Unit 42 said it’s tracking the cluster under the moniker CL-STA-1009, where “CL” stands for cluster and “STA” refers to state-backed motivation.
“Airstalk misuses the AirWatch API for mobile device management (MDM), which is now -
China-Linked Hackers Exploit Windows Shortcut Flaw to Target European Diplomats
A China-affiliated threat actor known as UNC6384 has been linked to a fresh set of attacks exploiting an unpatched Windows shortcut vulnerability to target European diplomatic and government entities between September and October 2025.
The activity targeted diplomatic organizations in Hungary, Belgium, Italy, and the Netherlands, as well as government agencies in Serbia, Arctic Wolf said in a