Social media platform X is urging users who have enrolled for two-factor authentication (2FA) using passkeys and hardware security keys like Yubikeys to re-enroll their key to ensure continued access to the service.
To that end, users are being asked to complete the re-enrollment, either using their existing security key or enrolling a new one, by November 10, 2025.
“After November 10, if you
Author: VanshTheHacker
-
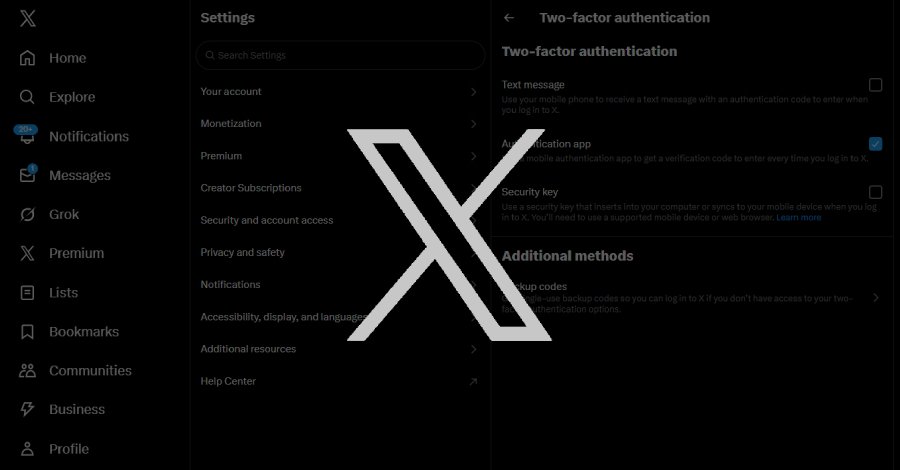
X Warns Users With Security Keys to Re-Enroll Before November 10 to Avoid Lockouts
-

⚡ Weekly Recap: WSUS Exploited, LockBit 5.0 Returns, Telegram Backdoor, F5 Breach Widens
Security, trust, and stability — once the pillars of our digital world — are now the tools attackers turn against us. From stolen accounts to fake job offers, cybercriminals keep finding new ways to exploit both system flaws and human behavior.
Each new breach proves a harsh truth: in cybersecurity, feeling safe can be far more dangerous than being alert.
Here’s how that false sense of security -
Qilin Ransomware Combines Linux Payload With BYOVD Exploit in Hybrid Attack
The ransomware group known as Qilin (aka Agenda, Gold Feather, and Water Galura) has claimed more than 40 victims every month since the start of 2025, barring January, with the number of postings on its data leak site touching a high of 100 cases in June.
The development comes as the ransomware-as-a-service (RaaS) operation has emerged as one of the most active ransomware groups, accounting for -
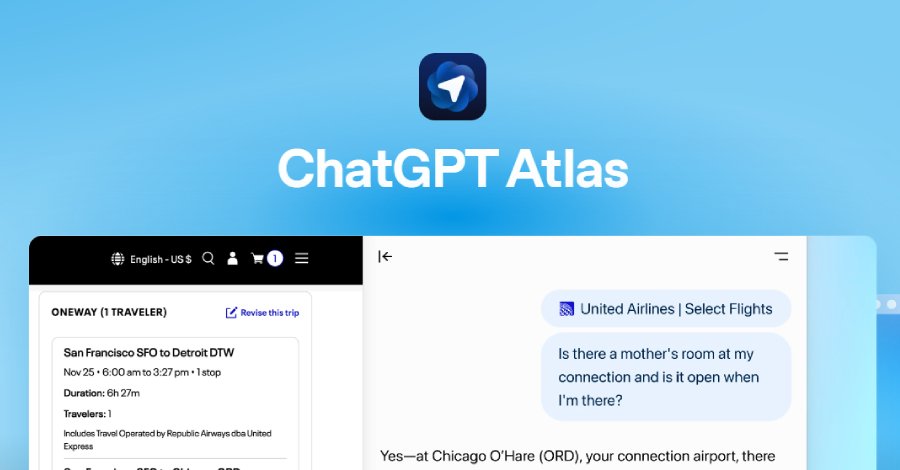
ChatGPT Atlas Browser Can Be Tricked by Fake URLs into Executing Hidden Commands
The newly released OpenAI Atlas web browser has been found to be susceptible to a prompt injection attack where its omnibox can be jailbroken by disguising a malicious prompt as a seemingly harmless URL to visit.
“The omnibox (combined address/search bar) interprets input either as a URL to navigate to, or as a natural-language command to the agent,” NeuralTrust said in a report published Friday -

Smishing Triad Linked to 194,000 Malicious Domains in Global Phishing Operation
The threat actors behind a large-scale, ongoing smishing campaign have been attributed to more than 194,000 malicious domains since January 1, 2024, targeting a broad range of services across the world, according to new findings from Palo Alto Networks Unit 42.
“Although these domains are registered through a Hong Kong-based registrar and use Chinese nameservers, the attack infrastructure is -

Newly Patched Critical Microsoft WSUS Flaw Comes Under Active Exploitation
Microsoft on Thursday released out-of-band security updates to patch a critical-severity Windows Server Update Service (WSUS) vulnerability with a proof-of-concept (Poc) exploit publicly available and has come under active exploitation in the wild.
The vulnerability in question is CVE-2025-59287 (CVSS score: 9.8), a remote code execution flaw in WSUS that was originally fixed by the tech giant -
EvilAI Malware Masquerades as AI Tools to Infiltrate Global Organizations
Threat actors have been observed using seemingly legitimate artificial intelligence (AI) tools and software to sneakily slip malware for future attacks on organizations worldwide.
According to Trend Micro, the campaign is using productivity or AI-enhanced tools to deliver malware targeting various regions, including Europe, the Americas, and the Asia, Middle East, and Africa (AMEA) region. -

⚡ Weekly Recap: Cisco 0-Day, Record DDoS, LockBit 5.0, BMC Bugs, ShadowV2 Botnet & More
Cybersecurity never stops—and neither do hackers. While you wrapped up last week, new attacks were already underway.
From hidden software bugs to massive DDoS attacks and new ransomware tricks, this week’s roundup gives you the biggest security moves to know. Whether you’re protecting key systems or locking down cloud apps, these are the updates you need before making your next security -

The State of AI in the SOC 2025 – Insights from Recent Study
Security leaders are embracing AI for triage, detection engineering, and threat hunting as alert volumes and burnout hit breaking points.
A comprehensive survey of 282 security leaders at companies across industries reveals a stark reality facing modern Security Operations Centers: alert volumes have reached unsustainable levels, forcing teams to leave critical threats uninvestigated. You can -

Microsoft Flags AI-Driven Phishing: LLM-Crafted SVG Files Outsmart Email Security
Microsoft is calling attention to a new phishing campaign primarily aimed at U.S.-based organizations that has likely utilized code generated using large language models (LLMs) to obfuscate payloads and evade security defenses.
“Appearing to be aided by a large language model (LLM), the activity obfuscated its behavior within an SVG file, leveraging business terminology and a synthetic structure