If this had been a security drill, someone would’ve said it went too far. But it wasn’t a drill—it was real. The access? Everything looked normal. The tools? Easy to find. The detection? Came too late.
This is how attacks happen now—quiet, convincing, and fast. Defenders aren’t just chasing hackers anymore—they’re struggling to trust what their systems are telling them.
The problem isn’t too
Author: VanshTheHacker
-

⚡ Weekly Recap: APT Intrusions, AI Malware, Zero-Click Exploits, Browser Hijacks and More
-
The Secret Defense Strategy of Four Critical Industries Combating Advanced Cyber Threats
The evolution of cyber threats has forced organizations across all industries to rethink their security strategies. As attackers become more sophisticated — leveraging encryption, living-off-the-land techniques, and lateral movement to evade traditional defenses — security teams are finding more threats wreaking havoc before they can be detected. Even after an attack has been identified, it can
-
New Linux Flaws Allow Password Hash Theft via Core Dumps in Ubuntu, RHEL, Fedora
Two information disclosure flaws have been identified in apport and systemd-coredump, the core dump handlers in Ubuntu, Red Hat Enterprise Linux, and Fedora, according to the Qualys Threat Research Unit (TRU).
Tracked as CVE-2025-5054 and CVE-2025-4598, both vulnerabilities are race condition bugs that could enable a local attacker to obtain access to access sensitive information. Tools like -

U.S. DoJ Seizes 4 Domains Supporting Cybercrime Crypting Services in Global Operation
A multinational law enforcement operation has resulted in the takedown of an online cybercrime syndicate that offered services to threat actors to ensure that their malicious software stayed undetected from security software.
To that effect, the U.S. Department of Justice (DoJ) said it seized four domains and their associated server facilitated the crypting service on May 27, 2025, in -
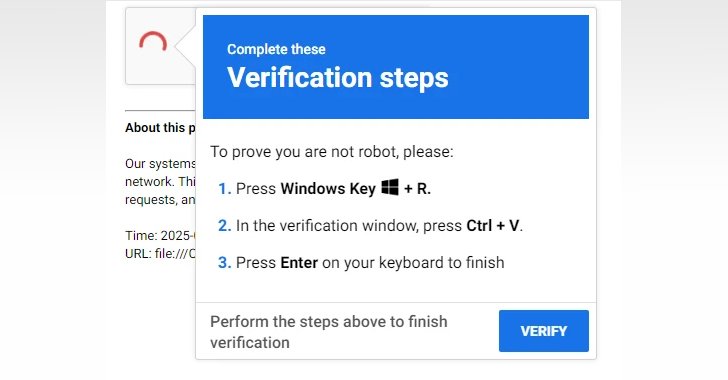
New EDDIESTEALER Malware Bypasses Chrome’s App-Bound Encryption to Steal Browser Data
A new malware campaign is distributing a novel Rust-based information stealer dubbed EDDIESTEALER using the popular ClickFix social engineering tactic initiated via fake CAPTCHA verification pages.
“This campaign leverages deceptive CAPTCHA verification pages that trick users into executing a malicious PowerShell script, which ultimately deploys the infostealer, harvesting sensitive data such as -

China-Linked Hackers Exploit SAP and SQL Server Flaws in Attacks Across Asia and Brazil
The China-linked threat actor behind the recent in-the-wild exploitation of a critical security flaw in SAP NetWeaver has been attributed to a broader set of attacks targeting organizations in Brazil, India, and Southeast Asia since 2023.
“The threat actor mainly targets the SQL injection vulnerabilities discovered on web applications to access the SQL servers of targeted organizations,” Trend -
From the “Department of No” to a “Culture of Yes”: A Healthcare CISO’s Journey to Enabling Modern Care
Breaking Out of the Security Mosh Pit
When Jason Elrod, CISO of MultiCare Health System, describes legacy healthcare IT environments, he doesn’t mince words: “Healthcare loves to walk backwards into the future. And this is how we got here, because there are a lot of things that we could have prepared for that we didn’t, because we were so concentrated on where we were.”
This chaotic approach has -

U.S. Sanctions Funnull for $200M Romance Baiting Scams Tied to Crypto Fraud
The U.S. Department of Treasury’s Office of Foreign Assets Control (OFAC) has levied sanctions against a Philippines-based company named Funnull Technology Inc. and its administrator Liu Lizhi for providing infrastructure to conduct romance baiting scams that led to massive cryptocurrency losses.
The Treasury accused the Taguig-headquartered company of enabling thousands of websites involved in -

ConnectWise Hit by Cyberattack; Nation-State Actor Suspected in Targeted Breach
ConnectWise, the developer of remote access and support software ScreenConnect, has disclosed that it was the victim of a cyber attack that it said was likely perpetrated by a nation-state threat actor.
“ConnectWise recently learned of suspicious activity within our environment that we believe was tied to a sophisticated nation-state actor, which affected a very small number of ScreenConnect -

Cybercriminals Target AI Users with Malware-Loaded Installers Posing as Popular Tools
Fake installers for popular artificial intelligence (AI) tools like OpenAI ChatGPT and InVideo AI are being used as lures to propagate various threats, such as the CyberLock and Lucky_Gh0$t ransomware families, and a new malware dubbed Numero.
“CyberLock ransomware, developed using PowerShell, primarily focuses on encrypting specific files on the victim’s system,” Cisco Talos researcher Chetan