Cybersecurity researchers have taken the wraps off an unusual cyber attack that leveraged malware with corrupted DOS and PE headers, according to new findings from Fortinet.
The DOS (Disk Operating System) and PE (Portable Executable) headers are essential parts of a Windows PE file, providing information about the executable.
While the DOS header makes the executable file backward compatible
Author: VanshTheHacker
-
New Windows RAT Evades Detection for Weeks Using Corrupted DOS and PE Headers
-

DragonForce Exploits SimpleHelp Flaws to Deploy Ransomware Across Customer Endpoints
The threat actors behind the DragonForce ransomware gained access to an unnamed Managed Service Provider’s (MSP) SimpleHelp remote monitoring and management (RMM) tool, and then leveraged it to exfiltrate data and drop the locker on multiple endpoints.
It’s believed that the attackers exploited a trio of security flaws in SimpleHelp (CVE-2024-57727, CVE-2024-57728, and CVE-2024-57726) that were -
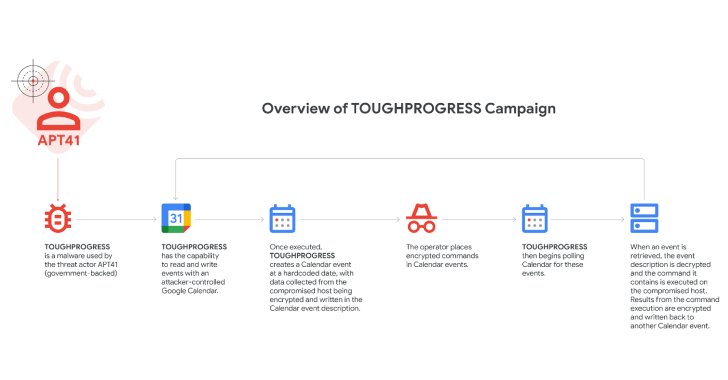
Chinese APT41 Exploits Google Calendar for Malware Command-and-Control Operations
Google on Wednesday disclosed that the Chinese state-sponsored threat actor known as APT41 leveraged a malware called TOUGHPROGRESS that uses Google Calendar for command-and-control (C2).
The tech giant, which discovered the activity in late October 2024, said the malware was hosted on a compromised government website and was used to target multiple other government entities.
“Misuse of cloud -

Over 100,000 WordPress Sites at Risk from Critical CVSS 10.0 Vulnerability in Wishlist Plugin
Cybersecurity researchers have disclosed a critical unpatched security flaw impacting TI WooCommerce Wishlist plugin for WordPress that could be exploited by unauthenticated attackers to upload arbitrary files.
TI WooCommerce Wishlist, which has over 100,000 active installations, is a tool to allow e-commerce site customers to save their favorite products for later and share the lists on social -
Iranian Hacker Pleads Guilty in $19 Million Robbinhood Ransomware Attack on Baltimore
An Iranian national has pleaded guilty in the U.S. over his involvement in an international ransomware and extortion scheme involving the Robbinhood ransomware.
Sina Gholinejad (aka Sina Ghaaf), 37, and his co-conspirators are said to have breached the computer networks of various organizations in the United States and encrypted files with Robbinhood ransomware to demand Bitcoin ransom payments. -

Czech Republic Blames China-Linked APT31 Hackers for 2022 Cyberattack
The Czech Republic on Wednesday formally accused a threat actor associated with the People’s Republic of China (PRC) of targeting its Ministry of Foreign Affairs.
In a public statement, the government said it identified China as the culprit behind a malicious campaign targeting one of the unclassified networks of the Czech Ministry of Foreign Affairs. The extent of the breach is presently not -

Microsoft OneDrive File Picker Flaw Grants Apps Full Cloud Access — Even When Uploading Just One File
Cybersecurity researchers have discovered a security flaw in Microsoft’s OneDrive File Picker that, if successfully exploited, could allow websites to access a user’s entire cloud storage content, as opposed to just the files selected for upload via the tool.
“This stems from overly broad OAuth scopes and misleading consent screens that fail to clearly explain the extent of access being granted, -

New PumaBot Botnet Targets Linux IoT Devices to Steal SSH Credentials and Mine Crypto
Embedded Linux-based Internet of Things (IoT) devices have become the target of a new botnet dubbed PumaBot.
Written in Go, the botnet is designed to conduct brute-force attacks against SSH instances to expand in size and scale and deliver additional malware to the infected hosts.
“Rather than scanning the internet, the malware retrieves a list of targets from a command-and-control (C2) server -

From Infection to Access: A 24-Hour Timeline of a Modern Stealer Campaign
Stealer malware no longer just steals passwords. In 2025, it steals live sessions—and attackers are moving faster and more efficiently than ever.
While many associate account takeovers with personal services, the real threat is unfolding in the enterprise. Flare’s latest research, The Account and Session Takeover Economy, analyzed over 20 million stealer logs and tracked attacker activity across -
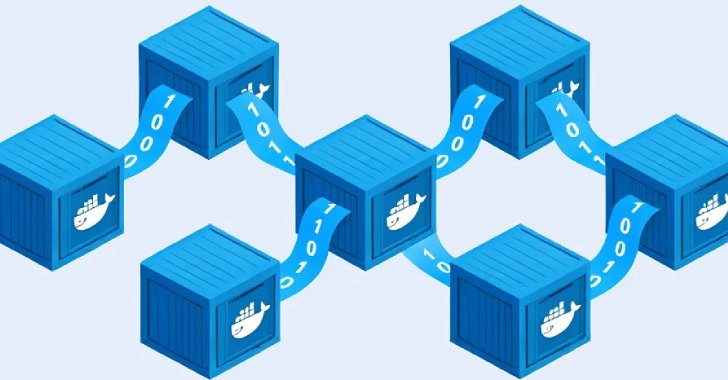
New Self-Spreading Malware Infects Docker Containers to Mine Dero Cryptocurrency
Misconfigured Docker API instances have become the target of a new malware campaign that transforms them into a cryptocurrency mining botnet.
The attacks, designed to mine for Dero currency, is notable for its worm-like capabilities to propagate the malware to other exposed Docker instances and rope them into an ever-growing horde of mining bots.
Kaspersky said it observed an unidentified threat