A Chinese-speaking threat actor tracked as UAT-6382 has been linked to the exploitation of a now-patched remote-code-execution vulnerability in Trimble Cityworks to deliver Cobalt Strike and VShell.
“UAT-6382 successfully exploited CVE-2025-0944, conducted reconnaissance, and rapidly deployed a variety of web shells and custom-made malware to maintain long-term access,” Cisco Talos researchers
Author: VanshTheHacker
-

Chinese Hackers Exploit Trimble Cityworks Flaw to Infiltrate U.S. Government Networks
-

Critical Windows Server 2025 dMSA Vulnerability Enables Active Directory Compromise
A privilege escalation flaw has been demonstrated in Windows Server 2025 that makes it possible for attackers to compromise any user in Active Directory (AD).
“The attack exploits the delegated Managed Service Account (dMSA) feature that was introduced in Windows Server 2025, works with the default configuration, and is trivial to implement,” Akamai security researcher Yuval Gordon said in a -

Chinese Hackers Exploit Ivanti EPMM Bugs in Global Enterprise Network Attacks
A recently patched pair of security flaws affecting Ivanti Endpoint Manager Mobile (EPMM) software has been exploited by a China-nexus threat actor to target a wide range of sectors across Europe, North America, and the Asia-Pacific region.
The vulnerabilities, tracked as CVE-2025-4427 (CVSS score: 5.3) and CVE-2025-4428 (CVSS score: 7.2), could be chained to execute arbitrary code on a -

Webinar: Learn How to Build a Reasonable and Legally Defensible Cybersecurity Program
It’s not enough to be secure. In today’s legal climate, you need to prove it.
Whether you’re protecting a small company or managing compliance across a global enterprise, one thing is clear: cybersecurity can no longer be left to guesswork, vague frameworks, or best-effort intentions.
Regulators and courts are now holding organizations accountable for how “reasonable” their security programs are -
Identity Security Has an Automation Problem—And It’s Bigger Than You Think
For many organizations, identity security appears to be under control. On paper, everything checks out. But new research from Cerby, based on insights from over 500 IT and security leaders, reveals a different reality: too much still depends on people—not systems—to function. In fact, fewer than 4% of security teams have fully automated their core identity workflows.
Core workflows, like -

Russian Hackers Exploit Email and VPN Vulnerabilities to Spy on Ukraine Aid Logistics
Russian cyber threat actors have been attributed to a state-sponsored campaign targeting Western logistics entities and technology companies since 2022.
The activity has been assessed to be orchestrated by APT28 (aka BlueDelta, Fancy Bear, or Forest Blizzard), which is linked to the Russian General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center, Military Unit 26165. -
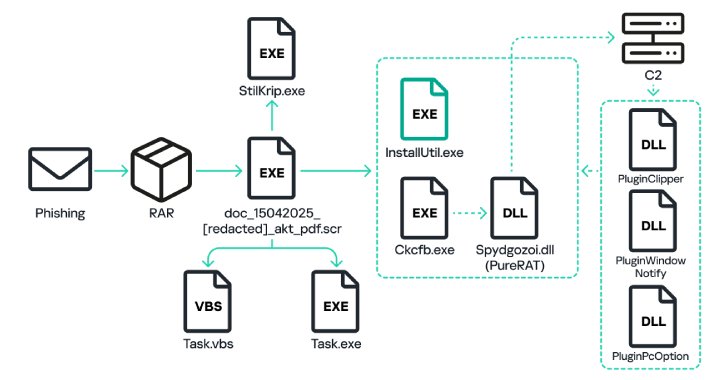
PureRAT Malware Spikes 4x in 2025, Deploying PureLogs to Target Russian Firms
Russian organizations have become the target of a phishing campaign that distributes malware called PureRAT, according to new findings from Kaspersky.
“The campaign aimed at Russian business began back in March 2023, but in the first third of 2025 the number of attacks quadrupled compared to the same period in 2024,” the cybersecurity vendor said.
The attack chains, which have not been -
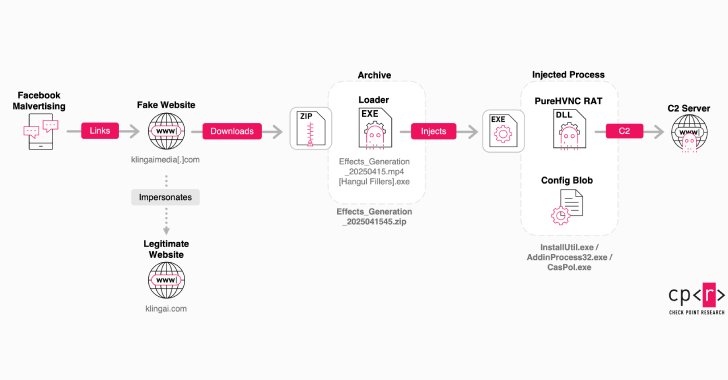
Fake Kling AI Facebook Ads Deliver RAT Malware to Over 22 Million Potential Victims
Counterfeit Facebook pages and sponsored ads on the social media platform are being employed to direct users to fake websites masquerading as Kling AI with the goal of tricking victims into downloading malware.
Kling AI is an artificial intelligence (AI)-powered platform to synthesize images and videos from text and image prompts. Launched in June 2024, it’s developed by Kuaishou Technology, -

Securing CI/CD workflows with Wazuh
Continuous Integration and Continuous Delivery/Deployment (CI/CD) refers to practices that automate how code is developed and released to different environments. CI/CD pipelines are fundamental in modern software development, ensuring code is consistently tested, built, and deployed quickly and efficiently.
While CI/CD automation accelerates software delivery, it can also introduce security -

How to Detect Phishing Attacks Faster: Tycoon2FA Example
It takes just one email to compromise an entire system. A single well-crafted message can bypass filters, trick employees, and give attackers the access they need. Left undetected, these threats can lead to credential theft, unauthorized access, and even full-scale breaches. As phishing techniques become more evasive, they can no longer be reliably caught by automated solutions alone.
Let’s take