Browsing Category
Data Breaches
1146 posts
Your blog category
⚡ Weekly Recap: AI Skill Malware, 31Tbps DDoS, Notepad++ Hack, LLM Backdoors and More
Cyber threats are no longer coming from just malware or exploits. They’re showing up inside the tools, platforms,…
February 9, 2026
How Top CISOs Solve Burnout and Speed up MTTR without Extra Hiring
Why do SOC teams keep burning out and missing SLAs even after spending big on security tools? Routine…
February 9, 2026
OpenClaw Integrates VirusTotal Scanning to Detect Malicious ClawHub Skills
OpenClaw (formerly Moltbot and Clawdbot) has announced that it’s partnering with Google-owned VirusTotal to scan skills that are…
February 8, 2026
German Agencies Warn of Signal Phishing Targeting Politicians, Military, Journalists
Germany’s Federal Office for the Protection of the Constitution (aka Bundesamt für Verfassungsschutz or BfV) and Federal Office…
February 7, 2026
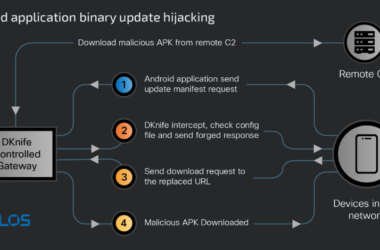
China-Linked DKnife AitM Framework Targets Routers for Traffic Hijacking, Malware Delivery
Cybersecurity researchers have taken the wraps off a gateway-monitoring and adversary-in-the-middle (AitM) framework dubbed DKnife that’s operated by…
February 6, 2026
CISA Orders Removal of Unsupported Edge Devices to Reduce Federal Network Risk
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has ordered Federal Civilian Executive Branch (FCEB) agencies to strengthen…
February 6, 2026
Asian State-Backed Group TGR-STA-1030 Breaches 70 Government, Infrastructure Entities
A previously undocumented cyber espionage group operating from Asia broke into the networks of at least 70 government…
February 6, 2026
How Samsung Knox Helps Stop Your Network Security Breach
As you know, enterprise network security has undergone significant evolution over the past decade. Firewalls have become more…
February 6, 2026
New MongoDB Flaw Lets Unauthenticated Attackers Read Uninitialized Memory
A high-severity security flaw has been disclosed in MongoDB that could allow unauthenticated users to read uninitialized heap…
December 27, 2025
Trust Wallet Chrome Extension Breach Caused $7 Million Crypto Loss via Malicious Code
Trust Wallet is urging users to update its Google Chrome extension to the latest version following what it…
December 26, 2025