Browsing Category
Data Breaches
1151 posts
Your blog category
CISA Flags Actively Exploited Digiever NVR Vulnerability Allowing Remote Code Execution
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a security flaw impacting Digiever DS-2105 Pro network video…
December 25, 2025
New MacSync macOS Stealer Uses Signed App to Bypass Apple Gatekeeper
Cybersecurity researchers have discovered a new variant of a macOS information stealer called MacSync that’s delivered by means…
December 24, 2025
Nomani Investment Scam Surges 62% Using AI Deepfake Ads on Social Media
The fraudulent investment scheme known as Nomani has witnessed an increase by 62%, according to data from ESET,…
December 24, 2025
Attacks are Evolving: 3 Ways to Protect Your Business in 2026
Every year, cybercriminals find new ways to steal money and data from businesses. Breaching a business network, extracting…
December 24, 2025
SEC Files Charges Over $14 Million Crypto Scam Using Fake AI-Themed Investment Tips
The U.S. Securities and Exchange Commission (SEC) has filed charges against multiple companies for their alleged involvement in…
December 24, 2025
Italy Fines Apple €98.6 Million Over ATT Rules Limiting App Store Competition
Apple has been fined €98.6 million ($116 million) by Italy’s antitrust authority after finding that the company’s App…
December 24, 2025
Two Chrome Extensions Caught Secretly Stealing Credentials from Over 170 Sites
Cybersecurity researchers have discovered two malicious Google Chrome extensions with the same name and published by the same…
December 23, 2025
INTERPOL Arrests 574 in Africa; Ukrainian Ransomware Affiliate Pleads Guilty
A law enforcement operation coordinated by INTERPOL has led to the recovery of $3 million and the arrest…
December 23, 2025
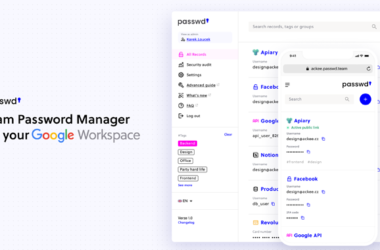
Passwd: A walkthrough of the Google Workspace Password Manager
Passwd is designed specifically for organizations operating within Google Workspace. Rather than competing as a general consumer password…
December 23, 2025
U.S. DoJ Seizes Fraud Domain Behind $14.6 Million Bank Account Takeover Scheme
The U.S. Justice Department (DoJ) on Monday announced the seizure of a web domain and database that it…
December 23, 2025