Browsing Category
Data Breaches
1151 posts
Your blog category
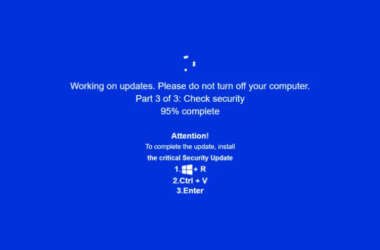
JackFix Uses Fake Windows Update Pop-Ups on Adult Sites to Deliver Multiple Stealers
Cybersecurity researchers are calling attention to a new campaign that’s leveraging a combination of ClickFix lures and fake…
November 25, 2025
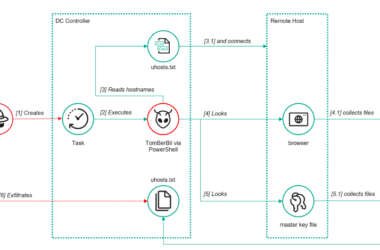
ToddyCat’s New Hacking Tools Steal Outlook Emails and Microsoft 365 Access Tokens
The threat actor known as ToddyCat has been observed adopting new methods to obtain access to corporate email…
November 25, 2025
3 SOC Challenges You Need to Solve Before 2026
2026 will mark a pivotal shift in cybersecurity. Threat actors are moving from experimenting with AI to making…
November 25, 2025
Hackers Hijack Blender 3D Assets to Deploy StealC V2 Data-Stealing Malware
Cybersecurity researchers have disclosed details of a new campaign that has leveraged Blender Foundation files to deliver an…
November 25, 2025
CISA Warns of Active Spyware Campaigns Hijacking High-Value Signal and WhatsApp Users
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday issued an alert warning of bad actors actively…
November 25, 2025
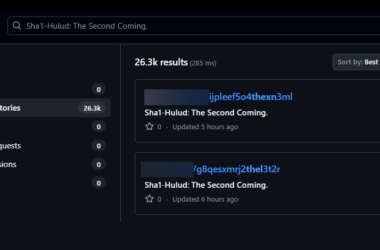
Second Sha1-Hulud Wave Affects 25,000+ Repositories via npm Preinstall Credential Theft
Multiple security vendors are sounding the alarm about a second wave of attacks targeting the npm registry in…
November 24, 2025
⚡ Weekly Recap: Fortinet Exploit, Chrome 0-Day, BadIIS Malware, Record DDoS, SaaS Breach & More
This week saw a lot of new cyber trouble. Hackers hit Fortinet and Chrome with new 0-day bugs.…
November 24, 2025
Chinese DeepSeek-R1 AI Generates Insecure Code When Prompts Mention Tibet or Uyghurs
New research from CrowdStrike has revealed that DeepSeek’s artificial intelligence (AI) reasoning model DeepSeek-R1 produces more security vulnerabilities…
November 24, 2025
ShadowPad Malware Actively Exploits WSUS Vulnerability for Full System Access
A recently patched security flaw in Microsoft Windows Server Update Services (WSUS) has been exploited by threat actors…
November 24, 2025
China-Linked APT31 Launches Stealthy Cyberattacks on Russian IT Using Cloud Services
The China-linked advanced persistent threat (APT) group known as APT31 has been attributed to cyber attacks targeting the…
November 22, 2025