Browsing Category
Data Breaches
1157 posts
Your blog category
Hackers Exploit Apache HTTP Server Flaw to Deploy Linuxsys Cryptocurrency Miner
Cybersecurity researchers have discovered a new campaign that exploits a known security flaw impacting Apache HTTP Server to…
July 17, 2025
Europol Disrupts NoName057(16) Hacktivist Group Linked to DDoS Attacks Against Ukraine
An international operation coordinated by Europol has disrupted the infrastructure of a pro-Russian hacktivist group known as NoName057(16)…
July 17, 2025
CTEM vs ASM vs Vulnerability Management: What Security Leaders Need to Know in 2025
The modern-day threat landscape requires enterprise security teams to think and act beyond traditional cybersecurity measures that are…
July 17, 2025
Chinese Hackers Target Taiwan’s Semiconductor Sector with Cobalt Strike, Custom Backdoors
The Taiwanese semiconductor industry has become the target of spear-phishing campaigns undertaken by three Chinese state-sponsored threat actors.…
July 17, 2025
Cisco Warns of Critical ISE Flaw Allowing Unauthenticated Attackers to Execute Root Code
Cisco has disclosed a new maximum-severity security vulnerability impacting Identity Services Engine (ISE) and Cisco ISE Passive Identity…
July 17, 2025
UNC6148 Backdoors Fully-Patched SonicWall SMA 100 Series Devices with OVERSTEP Rootkit
A threat activity cluster has been observed targeting fully-patched end-of-life SonicWall Secure Mobile Access (SMA) 100 series appliances…
July 16, 2025
Critical Golden dMSA Attack in Windows Server 2025 Enables Cross-Domain Attacks and Persistent Access
Cybersecurity researchers have disclosed what they say is a “critical design flaw” in delegated Managed Service Accounts (dMSAs)…
July 16, 2025
AI Agents Act Like Employees With Root Access—Here’s How to Regain Control
The AI gold rush is on. But without identity-first security, every deployment becomes an open door. Most organizations…
July 16, 2025
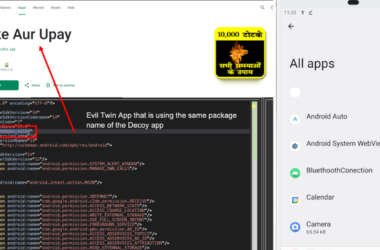
New Konfety Malware Variant Evades Detection by Manipulating APKs and Dynamic Code
Cybersecurity researchers have discovered a new, sophisticated variant of a known Android malware referred to as Konfety that…
July 16, 2025
Deepfakes. Fake Recruiters. Cloned CFOs — Learn How to Stop AI-Driven Attacks in Real Time
Social engineering attacks have entered a new era—and they’re coming fast, smart, and deeply personalized. It’s no longer…
July 16, 2025