Browsing Category
Data Breaches
1159 posts
Your blog category
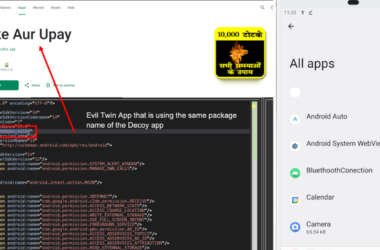
New Konfety Malware Variant Evades Detection by Manipulating APKs and Dynamic Code
Cybersecurity researchers have discovered a new, sophisticated variant of a known Android malware referred to as Konfety that…
July 16, 2025
Deepfakes. Fake Recruiters. Cloned CFOs — Learn How to Stop AI-Driven Attacks in Real Time
Social engineering attacks have entered a new era—and they’re coming fast, smart, and deeply personalized. It’s no longer…
July 16, 2025
State-Backed HazyBeacon Malware Uses AWS Lambda to Steal Data from SE Asian Governments
Governmental organizations in Southeast Asia are the target of a new campaign that aims to collect sensitive information…
July 15, 2025
Securing Agentic AI: How to Protect the Invisible Identity Access
AI agents promise to automate everything from financial reconciliations to incident response. Yet every time an AI agent…
July 15, 2025
AsyncRAT’s Open-Source Code Sparks Surge in Dangerous Malware Variants Across the Globe
Cybersecurity researchers have charted the evolution of a widely used remote access trojan called AsyncRAT, which was first…
July 15, 2025
North Korean Hackers Flood npm Registry with XORIndex Malware in Ongoing Attack Campaign
The North Korean threat actors linked to the Contagious Interview campaign have been observed publishing another set of…
July 15, 2025
The Unusual Suspect: Git Repos
While phishing and ransomware dominate headlines, another critical risk quietly persists across most enterprises: exposed Git repositories leaking…
July 14, 2025
⚡ Weekly Recap: Scattered Spider Arrests, Car Exploits, macOS Malware, Fortinet RCE and More
In cybersecurity, precision matters—and there’s little room for error. A small mistake, missed setting, or quiet misconfiguration can…
July 14, 2025
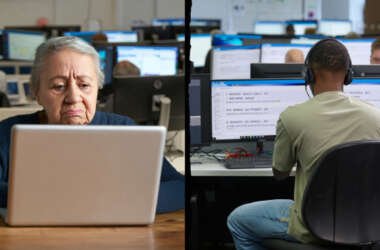
CBI Shuts Down £390K U.K. Tech Support Scam, Arrests Key Operatives in Noida Call Center
India’s Central Bureau of Investigation (CBI) has announced that it has taken steps to dismantle what it said…
July 14, 2025
eSIM Vulnerability in Kigen’s eUICC Cards Exposes Billions of IoT Devices to Malicious Attacks
Cybersecurity researchers have discovered a new hacking technique that exploits weaknesses in the eSIM technology used in modern…
July 14, 2025