Browsing Category
Data Breaches
1159 posts
Your blog category
GPUHammer: New RowHammer Attack Variant Degrades AI Models on NVIDIA GPUs
NVIDIA is urging customers to enable System-level Error Correction Codes (ECC) as a defense against a variant of…
July 12, 2025
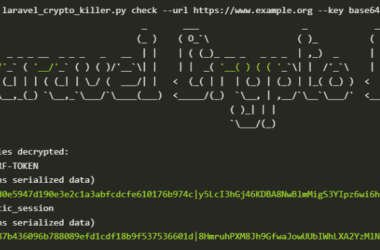
Over 600 Laravel Apps Exposed to Remote Code Execution Due to Leaked APP_KEYs on GitHub
Cybersecurity researchers have discovered a serious security issue that allows leaked Laravel APP_KEYs to be weaponized to gain…
July 12, 2025
Fortinet Releases Patch for Critical SQL Injection Flaw in FortiWeb (CVE-2025-25257)
Fortinet has released fixes for a critical security flaw impacting FortiWeb that could enable an unauthenticated attacker to…
July 11, 2025
PerfektBlue Bluetooth Vulnerabilities Expose Millions of Vehicles to Remote Code Execution
Cybersecurity researchers have discovered a set of four security flaws in OpenSynergy’s BlueSDK Bluetooth stack that, if successfully…
July 11, 2025
Securing Data in the AI Era
The 2025 Data Risk Report: Enterprises face potentially serious data loss risks from AI-fueled tools. Adopting a unified,…
July 11, 2025
Critical Wing FTP Server Vulnerability (CVE-2025-47812) Actively Being Exploited in the Wild
A recently disclosed maximum-severity security flaw impacting the Wing FTP Server has come under active exploitation in the…
July 11, 2025
Iranian-Backed Pay2Key Ransomware Resurfaces with 80% Profit Share for Cybercriminals
An Iranian-backed ransomware-as-a-service (RaaS) named Pay2Key has resurfaced in the wake of the Israel-Iran-U.S. conflict last month, offering…
July 11, 2025
CISA Adds Citrix NetScaler CVE-2025-5777 to KEV Catalog as Active Exploits Target Enterprises
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a critical security flaw impacting Citrix NetScaler…
July 11, 2025
Four Arrested in £440M Cyber Attack on Marks & Spencer, Co-op, and Harrods
The U.K. National Crime Agency (NCA) on Thursday announced that four people have been arrested in connection with…
July 10, 2025
What Security Leaders Need to Know About AI Governance for SaaS
Generative AI is not arriving with a bang, it’s slowly creeping into the software that companies already use…
July 10, 2025