Storm-1977 Hits Education Clouds with AzureChecker, Deploys 200+ Crypto Mining Containers
Microsoft has revealed that a threat actor it tracks as Storm-1977 has conducted password spraying attacks against cloud…
April 27, 2025
ToyMaker Uses LAGTOY to Sell Access to CACTUS Ransomware Gangs for Double Extortion
Cybersecurity researchers have detailed the activities of an initial access broker (IAB) dubbed ToyMaker that has been observed…
April 26, 2025
North Korean Hackers Spread Malware via Fake Crypto Firms and Job Interview Lures
North Korea-linked threat actors behind the Contagious Interview have set up front companies as a way to distribute…
April 25, 2025
New Critical SAP NetWeaver Flaw Exploited to Drop Web Shell, Brute Ratel Framework
Threat actors are likely exploiting a new vulnerability in SAP NetWeaver to upload JSP web shells with the…
April 25, 2025
Why NHIs Are Security’s Most Dangerous Blind Spot
When we talk about identity in cybersecurity, most people think of usernames, passwords, and the occasional MFA prompt.…
April 25, 2025
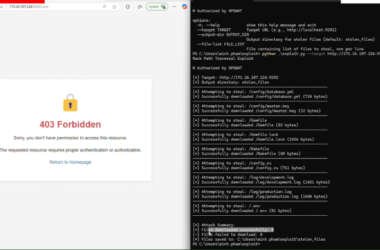
Researchers Identify Rack::Static Vulnerability Enabling Data Breaches in Ruby Servers
Cybersecurity researchers have disclosed three security flaws in the Rack Ruby web server interface that, if successfully exploited,…
April 25, 2025
DslogdRAT Malware Deployed via Ivanti ICS Zero-Day CVE-2025-0282 in Japan Attacks
Cybersecurity researchers are warning about a new malware called DslogdRAT that’s installed following the exploitation of a now-patched…
April 25, 2025
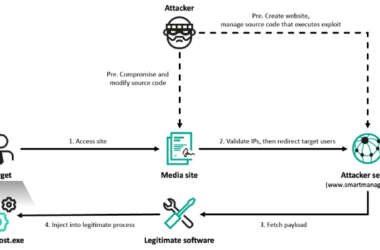
Lazarus Hits 6 South Korean Firms via Cross EX, Innorix Flaws and ThreatNeedle Malware
At least six organizations in South Korea have been targeted by the prolific North Korea-linked Lazarus Group as…
April 24, 2025
Linux io_uring PoC Rootkit Bypasses System Call-Based Threat Detection Tools
Cybersecurity researchers have demonstrated a proof-of-concept (PoC) rootkit dubbed Curing that leverages a Linux asynchronous I/O mechanism called…
April 24, 2025
Automating Zero Trust in Healthcare: From Risk Scoring to Dynamic Policy Enforcement Without Network Redesign
The Evolving Healthcare Cybersecurity Landscape Healthcare organizations face unprecedented cybersecurity challenges in 2025. With operational technology (OT) environments…
April 24, 2025