Three Reasons Why the Browser is Best for Stopping Phishing Attacks
Phishing attacks remain a huge challenge for organizations in 2025. In fact, with attackers increasingly leveraging identity-based techniques…
April 23, 2025
Russian Hackers Exploit Microsoft OAuth to Target Ukraine Allies via Signal and WhatsApp
Multiple suspected Russia-linked threat actors are “aggressively” targeting individuals and organizations with ties to Ukraine and human rights…
April 23, 2025
Docker Malware Exploits Teneo Web3 Node to Earn Crypto via Fake Heartbeat Signals
Cybersecurity researchers have detailed a malware campaign that’s targeting Docker environments with a previously undocumented technique to mine…
April 22, 2025
GCP Cloud Composer Bug Let Attackers Elevate Access via Malicious PyPI Packages
Cybersecurity researchers have detailed a now-patched vulnerability in Google Cloud Platform (GCP) that could have enabled an attacker…
April 22, 2025
5 Major Concerns With Employees Using The Browser
As SaaS and cloud-native work reshape the enterprise, the web browser has emerged as the new endpoint. However,…
April 22, 2025
Phishers Exploit Google Sites and DKIM Replay to Send Signed Emails, Steal Credentials
In what has been described as an “extremely sophisticated phishing attack,” threat actors have leveraged an uncommon approach…
April 22, 2025
Microsoft Secures MSA Signing with Azure Confidential VMs Following Storm-0558 Breach
Microsoft on Monday announced that it has moved the Microsoft Account (MSA) signing service to Azure confidential virtual…
April 22, 2025
Kimsuky Exploits BlueKeep RDP Vulnerability to Breach Systems in South Korea and Japan
Cybersecurity researchers have flagged a new malicious campaign related to the North Korean state-sponsored threat actor known as…
April 21, 2025
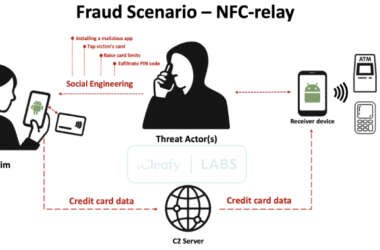
SuperCard X Android Malware Enables Contactless ATM and PoS Fraud via NFC Relay Attacks
A new Android malware-as-a-service (MaaS) platform named SuperCard X can facilitate near-field communication (NFC) relay attacks, enabling cybercriminals…
April 21, 2025
5 Reasons Device Management Isn’t Device Trust
The problem is simple: all breaches start with initial access, and initial access comes down to two primary…
April 21, 2025