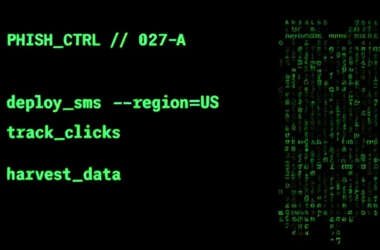
Chinese Smishing Kit Powers Widespread Toll Fraud Campaign Targeting U.S. Users in 8 States
Cybersecurity researchers are warning of a “widespread and ongoing” SMS phishing campaign that’s been targeting toll road users…
April 18, 2025
Multi-Stage Malware Attack Uses .JSE and PowerShell to Deploy Agent Tesla and XLoader
A new multi-stage attack has been observed delivering malware families like Agent Tesla variants, Remcos RAT, and XLoader.…
April 18, 2025
[Webinar] AI Is Already Inside Your SaaS Stack — Learn How to Prevent the Next Silent Breach
Your employees didn’t mean to expose sensitive data. They just wanted to move faster. So they used ChatGPT…
April 18, 2025
Experts Uncover New XorDDoS Controller, Infrastructure as Malware Expands to Docker, Linux, IoT
Cybersecurity researchers are warning of continued risks posed by a distributed denial-of-service (DDoS) malware known as XorDDoS, with…
April 18, 2025
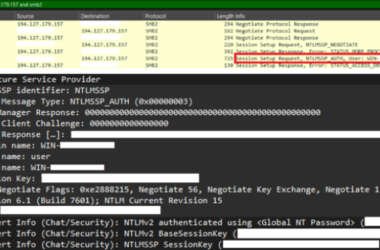
CVE-2025-24054 Under Active Attack—Steals NTLM Credentials on File Download
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a medium-severity security flaw impacting Microsoft Windows…
April 18, 2025
Mustang Panda Targets Myanmar With StarProxy, EDR Bypass, and TONESHELL Updates
The China-linked threat actor known as Mustang Panda has been attributed to a cyber attack targeting an unspecified…
April 17, 2025
State-Sponsored Hackers Weaponize ClickFix Tactic in Targeted Malware Campaigns
Multiple state-sponsored hacking groups from Iran, North Korea, and Russia have been found leveraging the increasingly popular ClickFix…
April 17, 2025
Artificial Intelligence – What’s all the fuss?
Talking about AI: Definitions Artificial Intelligence (AI) — AI refers to the simulation of human intelligence in machines,…
April 17, 2025
Critical Erlang/OTP SSH Vulnerability (CVSS 10.0) Allows Unauthenticated Code Execution
A critical security vulnerability has been disclosed in the Erlang/Open Telecom Platform (OTP) SSH implementation that could permit…
April 17, 2025
Blockchain Offers Security Benefits – But Don’t Neglect Your Passwords
Blockchain is best known for its use in cryptocurrencies like Bitcoin, but it also holds significant applications for…
April 17, 2025