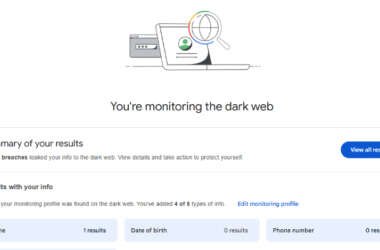
Google to Shut Down Dark Web Monitoring Tool in February 2026
Google has announced that it’s discontinuing its dark web report tool in February 2026, less than two years…
December 16, 2025
Featured Chrome Browser Extension Caught Intercepting Millions of Users’ AI Chats
A Google Chrome extension with a “Featured” badge and six million users has been observed silently gathering every…
December 15, 2025
FreePBX Patches Critical SQLi, File-Upload, and AUTHTYPE Bypass Flaws Enabling RCE
Multiple security vulnerabilities have been disclosed in the open-source private branch exchange (PBX) platform FreePBX, including a critical…
December 15, 2025
⚡ Weekly Recap: Apple 0-Days, WinRAR Exploit, LastPass Fines, .NET RCE, OAuth Scams & More
If you use a smartphone, browse the web, or unzip files on your computer, you are in the…
December 15, 2025
Phantom Stealer Spread by ISO Phishing Emails Hitting Russian Finance Sector
Cybersecurity researchers have disclosed details of an active phishing campaign that’s targeting a wide range of sectors in…
December 15, 2025
VolkLocker Ransomware Exposed by Hard-Coded Master Key Allowing Free Decryption
The pro-Russian hacktivist group known as CyberVolk (aka GLORIAMIST) has resurfaced with a new ransomware-as-a-service (RaaS) offering called…
December 15, 2025
CISA Adds Actively Exploited Sierra Wireless Router Flaw Enabling RCE Attacks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a high-severity flaw impacting Sierra Wireless AirLink…
December 13, 2025
Apple Issues Security Updates After Two WebKit Flaws Found Exploited in the Wild
Apple on Friday released security updates for iOS, iPadOS, macOS, tvOS, watchOS, visionOS, and its Safari web browser…
December 13, 2025
Fake OSINT and GPT Utility GitHub Repos Spread PyStoreRAT Malware Payloads
Cybersecurity researchers are calling attention to a new campaign that’s leveraging GitHub-hosted Python repositories to distribute a previously…
December 12, 2025
New Advanced Phishing Kits Use AI and MFA Bypass Tactics to Steal Credentials at Scale
Cybersecurity researchers have documented four new phishing kits named BlackForce, GhostFrame, InboxPrime AI, and Spiderman that are capable…
December 12, 2025