Researchers Detect Malicious npm Package Targeting GitHub-Owned Repositories
Cybersecurity researchers have discovered a malicious npm package named “@acitons/artifact” that typosquats the legitimate “@actions/artifact” package with the…
November 11, 2025
Android Trojan ‘Fantasy Hub’ Malware Service Turns Telegram Into a Hub for Hackers
Cybersecurity researchers have disclosed details of a new Android remote access trojan (RAT) called Fantasy Hub that’s sold…
November 11, 2025
Hackers Exploiting Triofox Flaw to Install Remote Access Tools via Antivirus Feature
Google’s Mandiant Threat Defense on Monday said it discovered n-day exploitation of a now-patched security flaw in Gladinet’s…
November 10, 2025
Konni Hackers Turn Google’s Find Hub into a Remote Data-Wiping Weapon
The North Korea-affiliated threat actor known as Konni (aka Earth Imp, Opal Sleet, Osmium, TA406, and Vedalia) has…
November 10, 2025
⚡ Weekly Recap: Hyper-V Malware, Malicious AI Bots, RDP Exploits, WhatsApp Lockdown and More
Cyber threats didn’t slow down last week—and attackers are getting smarter. We’re seeing malware hidden in virtual machines,…
November 10, 2025
New Browser Security Report Reveals Emerging Threats for Enterprises
According to the new Browser Security Report 2025, security leaders are discovering that most identity, SaaS, and AI-related…
November 10, 2025
Large-Scale ClickFix Phishing Attacks Target Hotel Systems with PureRAT Malware
Cybersecurity researchers have called attention to a massive phishing campaign targeting the hospitality industry that lures hotel managers…
November 10, 2025
GlassWorm Malware Discovered in Three VS Code Extensions with Thousands of Installs
Cybersecurity researchers have disclosed a new set of three extensions associated with the GlassWorm campaign, indicating continued attempts…
November 10, 2025
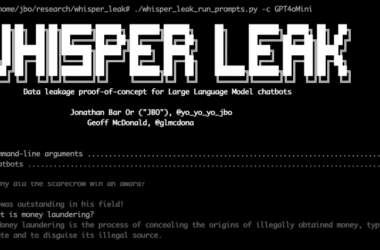
Microsoft Uncovers ‘Whisper Leak’ Attack That Identifies AI Chat Topics in Encrypted Traffic
Microsoft has disclosed details of a novel side-channel attack targeting remote language models that could enable a passive…
November 8, 2025
Samsung Mobile Flaw Exploited as Zero-Day to Deploy LANDFALL Android Spyware
A now-patched security flaw in Samsung Galaxy Android devices was exploited as a zero-day to deliver a “commercial-grade”…
November 7, 2025