Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit
A high-severity security flaw affecting default installations of Ubuntu Desktop versions 24.04 and later could be exploited to…
March 18, 2026
Apple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS
Apple on Tuesday released its first round of Background Security Improvements to address a security flaw in WebKit…
March 18, 2026
Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE via Port 23
Cybersecurity researchers have disclosed a critical security flaw impacting the GNU InetUtils telnet daemon (telnetd) that could be…
March 18, 2026
AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE
Cybersecurity researchers have disclosed details of a new method for exfiltrating sensitive data from artificial intelligence (AI) code…
March 17, 2026
AI is Everywhere, But CISOs are Still Securing It with Yesterday’s Skills and Tools, Study Finds
A majority of security leaders are struggling to defend AI systems with tools and skills that are not…
March 17, 2026
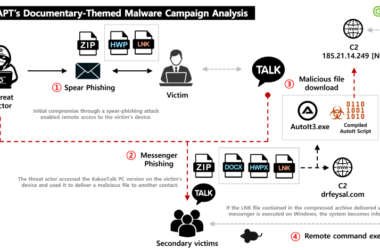
Konni Deploys EndRAT Through Phishing, Uses KakaoTalk to Propagate Malware
North Korean threat actors have been observed sending phishing to compromise targets and obtain access to a victim’s…
March 17, 2026
CISA Flags Actively Exploited Wing FTP Vulnerability Leaking Server Paths
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Wing FTP…
March 17, 2026
GlassWorm Attack Uses Stolen GitHub Tokens to Force-Push Malware Into Python Repos
The GlassWorm malware campaign is being used to fuel an ongoing attack that leverages the stolen GitHub tokens…
March 16, 2026
⚡ Weekly Recap: Chrome 0-Days, Router Botnets, AWS Breach, Rogue AI Agents & More
Some weeks in security feel normal. Then you read a few tabs and get that immediate “ah, great,…
March 16, 2026
DRILLAPP Backdoor Targets Ukraine, Abuses Microsoft Edge Debugging for Stealth Espionage
Ukrainian entities have emerged as the target of a new campaign likely orchestrated by threat actors linked to…
March 16, 2026