How to Gain Control of AI Agents and Non-Human Identities
We hear this a lot: “We’ve got hundreds of service accounts and AI agents running in the background.…
September 22, 2025
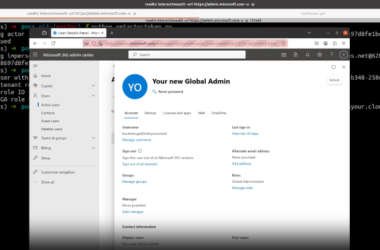
Microsoft Patches Critical Entra ID Flaw Enabling Global Admin Impersonation Across Tenants
A critical token validation failure in Microsoft Entra ID (previously Azure Active Directory) could have allowed attackers to…
September 22, 2025
DPRK Hackers Use ClickFix to Deliver BeaverTail Malware in Crypto Job Scams
Threat actors with ties to the Democratic People’s Republic of Korea (aka DPRK or North Korea) have been…
September 21, 2025
LastPass Warns of Fake Repositories Infecting macOS with Atomic Infostealer
LastPass is warning of an ongoing, widespread information stealer campaign targeting Apple macOS users through fake GitHub repositories…
September 20, 2025
Researchers Uncover GPT-4-Powered MalTerminal Malware Creating Ransomware, Reverse Shell
Cybersecurity researchers have discovered what they say is the earliest example known to date of a malware with…
September 20, 2025
ShadowLeak Zero-Click Flaw Leaks Gmail Data via OpenAI ChatGPT Deep Research Agent
Cybersecurity researchers have disclosed a zero-click flaw in OpenAI ChatGPT’s Deep Research agent that could allow an attacker…
September 20, 2025
UNC1549 Hacks 34 Devices in 11 Telecom Firms via LinkedIn Job Lures and MINIBIKE Malware
An Iran-nexus cyber espionage group known as UNC1549 has been attributed to a new campaign targeting European telecommunications…
September 19, 2025
SystemBC Powers REM Proxy With 1,500 Daily VPS Victims Across 80 C2 Servers
A proxy network known as REM Proxy is powered by malware known as SystemBC, offering about 80% of…
September 19, 2025
Fortra Releases Critical Patch for CVSS 10.0 GoAnywhere MFT Vulnerability
Fortra has disclosed details of a critical security flaw in GoAnywhere Managed File Transfer (MFT) software that could…
September 19, 2025
17,500 Phishing Domains Target 316 Brands Across 74 Countries in Global PhaaS Surge
The phishing-as-a-service (PhaaS) offering known as Lighthouse and Lucid has been linked to more than 17,500 phishing domains…
September 19, 2025