Authorities Disrupt SocksEscort Proxy Botnet Exploiting 369,000 IPs Across 163 Countries
A court-authorized international law enforcement operation has dismantled a criminal proxy service named SocksEscort that enslaved thousands of…
March 13, 2026
Veeam Patches 7 Critical Backup & Replication Flaws Allowing Remote Code Execution
Veeam has released security updates to address multiple critical vulnerabilities in its Backup & Replication software that, if…
March 13, 2026
Rust-Based VENON Malware Targets 33 Brazilian Banks with Credential-Stealing Overlays
Cybersecurity researchers have disclosed details of a new banking malware targeting Brazilian users that’s written in Rust, marking…
March 12, 2026
Apple Issues Security Updates for Older iOS Devices Targeted by Coruna WebKit Exploit
Apple on Wednesday backported fixes for a security flaw in iOS, iPadOS, and macOS Sonoma to older versions…
March 12, 2026
Six Android Malware Families Target Pix Payments, Banking Apps, and Crypto Wallets
Cybersecurity researchers have discovered half-a-dozen new Android malware families that come with capabilities to steal data from compromised…
March 12, 2026
CISA Flags Actively Exploited n8n RCE Bug as 24,700 Instances Remain Exposed
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a critical security flaw impacting n8n to…
March 12, 2026
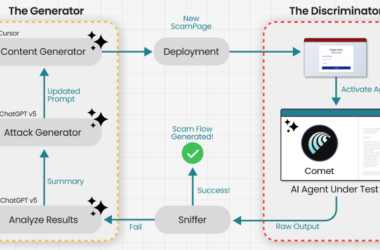
Researchers Trick Perplexity’s Comet AI Browser Into Phishing Scam in Under Four Minutes
Agentic web browsers that leverage artificial intelligence (AI) capabilities to autonomously execute actions across multiple websites on behalf…
March 11, 2026
Critical n8n Flaws Allow Remote Code Execution and Exposure of Stored Credentials
Cybersecurity researchers have disclosed details of two now-patched security flaws in the n8n workflow automation platform, including two…
March 11, 2026
Microsoft Patches 84 Flaws in March Patch Tuesday, Including Two Public Zero-Days
Microsoft on Tuesday released patches for a set of 84 new security vulnerabilities affecting various software components, including…
March 11, 2026
UNC6426 Exploits nx npm Supply-Chain Attack to Gain AWS Admin Access in 72 Hours
A threat actor known as UNC6426 leveraged keys stolen following the supply chain compromise of the nx npm…
March 11, 2026