Five Malicious Rust Crates and AI Bot Exploit CI/CD Pipelines to Steal Developer Secrets
Cybersecurity researchers have discovered five malicious Rust crates that masquerade as time-related utilities to transmit .env file data…
March 11, 2026
How to Stop AI Data Leaks: A Webinar Guide to Auditing Modern Agentic Workflows
Artificial Intelligence (AI) is no longer just a tool we talk to; it is a tool that does…
March 10, 2026
FortiGate Devices Exploited to Breach Networks and Steal Service Account Credentials
Cybersecurity researchers are calling attention to a new campaign where threat actors are abusing FortiGate Next-Generation Firewall (NGFW)…
March 10, 2026
Threat Actors Mass-Scan Salesforce Experience Cloud via Modified AuraInspector Tool
Salesforce has warned of an increase in threat actor activity that’s aimed at exploiting misconfigurations in publicly accessible…
March 10, 2026
CISA Flags SolarWinds, Ivanti, and Workspace One Vulnerabilities as Actively Exploited
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added three security flaws to its Known Exploited…
March 10, 2026
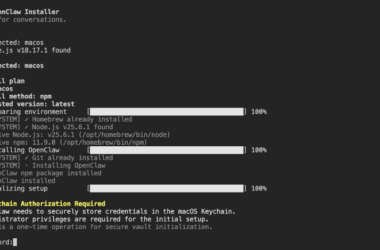
Malicious npm Package Posing as OpenClaw Installer Deploys RAT, Steals macOS Credentials
Cybersecurity researchers have discovered a malicious npm package that masquerades as an OpenClaw installer to deploy a remote…
March 9, 2026
UNC4899 Breached Crypto Firm After Developer AirDropped Trojanized File to Work Device
The North Korean threat actor known as UNC4899 is suspected to be behind a sophisticated cloud compromise campaign…
March 9, 2026
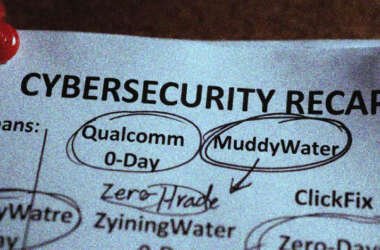
⚡ Weekly Recap: Qualcomm 0-Day, iOS Exploit Chains, AirSnitch Attack & Vibe-Coded Malware
Another week in cybersecurity. Another week of “you’ve got to be kidding me.” Attackers were busy. Defenders were…
March 9, 2026
Chrome Extension Turns Malicious After Ownership Transfer, Enabling Code Injection and Data Theft
Two Google Chrome extensions have turned malicious after what appears to be a case of ownership transfer, offering…
March 9, 2026
Web Server Exploits and Mimikatz Used in Attacks Targeting Asian Critical Infrastructure
High-value organizations located in South, Southeast, and East Asia have been targeted by a Chinese threat actor as…
March 9, 2026