TeamPCP Pushes Malicious Telnyx Versions to PyPI, Hides Stealer in WAV Files
TeamPCP, the threat actor behind the supply chain attack targeting Trivy, KICS, and litellm, has now compromised the…
March 27, 2026
We Are At War
Rising geopolitical tensions are reflected (or in some cases preceded) by cyber operations, while technology itself has become…
March 27, 2026
Bearlyfy Hits 70+ Russian Firms with Custom GenieLocker Ransomware
A pro-Ukrainian group called Bearlyfy has been attributed to more than 70 cyber attacks targeting Russian companies since…
March 27, 2026
LangChain, LangGraph Flaws Expose Files, Secrets, Databases in Widely Used AI Frameworks
Cybersecurity researchers have disclosed three security vulnerabilities impacting LangChain and LangGraph that, if successfully exploited, could expose filesystem…
March 27, 2026
China-Linked Red Menshen Uses Stealthy BPFDoor Implants to Spy via Telecom Networks
A long-term and ongoing campaign attributed to a China-nexus threat actor has embedded itself in telecom networks to…
March 26, 2026
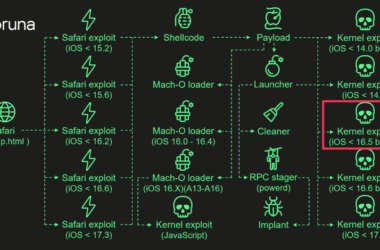
Coruna iOS Kit Reuses 2023 Triangulation Exploit Code in New Mass Attacks
The kernel exploit for two security vulnerabilities used in the recently uncovered Apple iOS exploit kit known as…
March 26, 2026
[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks
Most teams have security tools in place. Alerts are firing, dashboards look clean, threat intel is flowing in.…
March 26, 2026
WebRTC Skimmer Bypasses CSP to Steal Payment Data from E-Commerce Sites
Cybersecurity researchers have discovered a new payment skimmer that uses WebRTC data channels as a means to receive…
March 26, 2026
LeakBase Admin Arrested in Russia Over Massive Stolen Credential Marketplace
The alleged administrator of the LeakBase cybercrime forum has been arrested by Russian law enforcement authorities, state media…
March 25, 2026
GlassWorm Malware Uses Solana Dead Drops to Deliver RAT and Steal Browser, Crypto Data
Cybersecurity researchers have flagged a new evolution of the GlassWorm campaign that delivers a multi-stage framework capable of…
March 25, 2026