Google Adds Multi-Layered Defenses to Secure GenAI from Prompt Injection Attacks
Google has revealed the various safety measures that are being incorporated into its generative artificial intelligence (AI) systems…
June 23, 2025
⚡ Weekly Recap: Chrome 0-Day, 7.3 Tbps DDoS, MFA Bypass Tricks, Banking Trojan and More
Not every risk looks like an attack. Some problems start as small glitches, strange logs, or quiet delays…
June 23, 2025
Scattered Spider Behind Cyberattacks on M&S and Co-op, Causing Up to $592M in Damages
The April 2025 cyber attacks targeting U.K. retailers Marks & Spencer and Co-op have been classified as a…
June 21, 2025
Qilin Ransomware Adds “Call Lawyer” Feature to Pressure Victims for Larger Ransoms
The threat actors behind the Qilin ransomware-as-a-service (RaaS) scheme are now offering legal counsel for affiliates to put…
June 20, 2025
Iran’s State TV Hijacked Mid-Broadcast Amid Geopolitical Tensions; $90M Stolen in Crypto Heist
Iran’s state-owned TV broadcaster was hacked Wednesday night to interrupt regular programming and air videos calling for street…
June 20, 2025
6 Steps to 24/7 In-House SOC Success
Hackers never sleep, so why should enterprise defenses? Threat actors prefer to target businesses during off-hours. That’s when…
June 20, 2025
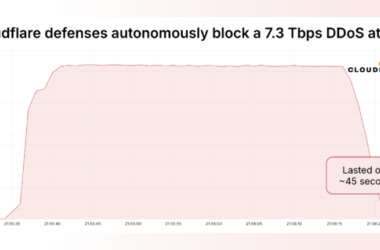
Massive 7.3 Tbps DDoS Attack Delivers 37.4 TB in 45 Seconds, Targeting Hosting Provider
Cloudflare on Thursday said it autonomously blocked the largest ever distributed denial-of-service (DDoS) attack ever recorded, which hit…
June 20, 2025
200+ Trojanized GitHub Repositories Found in Campaign Targeting Gamers and Developers
Cybersecurity researchers have uncovered a new campaign in which the threat actors have published more than 67 GitHub…
June 20, 2025
New Android Malware Surge Hits Devices via Overlays, Virtualization Fraud and NFC Theft
Cybersecurity researchers have exposed the inner workings of an Android malware called AntiDot that has compromised over 3,775…
June 19, 2025
BlueNoroff Deepfake Zoom Scam Hits Crypto Employee with MacOS Backdoor Malware
The North Korea-aligned threat actor known as BlueNoroff has been observed targeting an employee in the Web3 sector…
June 19, 2025