Another week in cybersecurity. Another week of “you’ve got to be kidding me.”
Attackers were busy. Defenders were busy. And somewhere in the middle, a whole lot of people had a very bad Monday morning. That’s kind of just how it goes now.
The good news? There were some actual wins this week. Real ones. The kind where the good guys showed up, did the work, and made a dent. It doesn’t always
Author: VanshTheHacker
-
⚡ Weekly Recap: Qualcomm 0-Day, iOS Exploit Chains, AirSnitch Attack & Vibe-Coded Malware
-

Chrome Extension Turns Malicious After Ownership Transfer, Enabling Code Injection and Data Theft
Two Google Chrome extensions have turned malicious after what appears to be a case of ownership transfer, offering attackers a way to push malware to downstream customers, inject arbitrary code, and harvest sensitive data.
The extensions in question, both originally associated with a developer named “akshayanuonline@gmail.com” (BuildMelon), are listed below –QuickLens – Search Screen with
-
Web Server Exploits and Mimikatz Used in Attacks Targeting Asian Critical Infrastructure
High-value organizations located in South, Southeast, and East Asia have been targeted by a Chinese threat actor as part of a years-long campaign.
The activity, which has targeted aviation, energy, government, law enforcement, pharmaceutical, technology, and telecommunications sectors, has been attributed by Palo Alto Networks Unit 42 to a previously undocumented threat activity group dubbed -
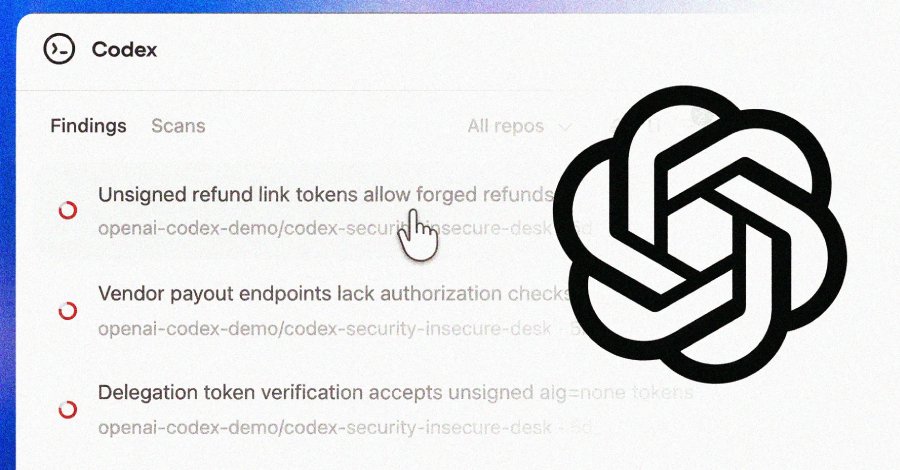
OpenAI Codex Security Scanned 1.2 Million Commits and Found 10,561 High-Severity Issues
OpenAI on Friday began rolling out Codex Security, an artificial intelligence (AI)-powered security agent that’s designed to find, validate, and propose fixes for vulnerabilities.
The feature is available in a research preview to ChatGPT Pro, Enterprise, Business, and Edu customers via the Codex web with free usage for the next month.
“It builds deep context about your project to identify -

Anthropic Finds 22 Firefox Vulnerabilities Using Claude Opus 4.6 AI Model
Anthropic on Friday said it discovered 22 new security vulnerabilities in the Firefox web browser as part of a security partnership with Mozilla.
Of these, 14 have been classified as high, seven have been classified as moderate, and one has been rated low in severity. The issues were addressed in Firefox 148, released late last month. The vulnerabilities were identified over a two-week period in -
Transparent Tribe Uses AI to Mass-Produce Malware Implants in Campaign Targeting India
The Pakistan-aligned threat actor known as Transparent Tribe has become the latest hacking group to embrace artificial intelligence (AI)-powered coding tools to strike targets with various implants.
The activity is designed to produce a “high-volume, mediocre mass of implants” that are developed using lesser-known programming languages like Nim, Zig, and Crystal and rely on trusted services like -

Multi-Stage VOID#GEIST Malware Delivering XWorm, AsyncRAT, and Xeno RAT
Cybersecurity researchers have disclosed details of a multi-stage malware campaign that uses batch scripts as a pathway to deliver various encrypted remote access trojan (RATs) payloads that correspond to XWorm, AsyncRAT, and Xeno RAT.
The stealthy attack chain has been codenamed VOID#GEIST by Securonix Threat Research.
At a high level, the obfuscated batch script is used to deploy a second -

The MSP Guide to Using AI-Powered Risk Management to Scale Cybersecurity
Scaling cybersecurity services as an MSP or MSSP requires technical expertise and a business model that delivers measurable value at scale.
Risk-based cybersecurity is the foundation of that model. When done right, it builds client trust, increases upsell opportunities, and drives recurring revenue. But to deliver this consistently and efficiently, you need the right technology and processes. -

Iran-Linked MuddyWater Hackers Target U.S. Networks With New Dindoor Backdoor
New research from Broadcom’s Symantec and Carbon Black Threat Hunter Team has discovered evidence of an Iranian hacking group embedding itself in several U.S. companies’ networks, including banks, airports, non-profit, and the Israeli arm of a software company.
The activity has been attributed to a state-sponsored hacking group called MuddyWater (aka Seedworm). It’s affiliated with the Iranian -

China-Linked Hackers Use TernDoor, PeerTime, BruteEntry in South American Telecom Attacks
A China-linked advanced persistent threat (APT) actor has been targeting critical telecommunications infrastructure in South America since 2024, targeting Windows and Linux systems and edge devices with three different implants.
The activity is being tracked by Cisco Talos under the moniker UAT-9244, describing it as closely associated with another cluster known as FamousSparrow.
It’s worth