Browsing Category
Data Breaches
1151 posts
Your blog category
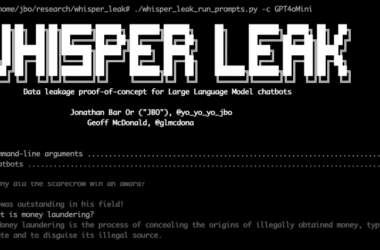
Microsoft Uncovers ‘Whisper Leak’ Attack That Identifies AI Chat Topics in Encrypted Traffic
Microsoft has disclosed details of a novel side-channel attack targeting remote language models that could enable a passive…
November 8, 2025
Samsung Mobile Flaw Exploited as Zero-Day to Deploy LANDFALL Android Spyware
A now-patched security flaw in Samsung Galaxy Android devices was exploited as a zero-day to deliver a “commercial-grade”…
November 7, 2025
From Log4j to IIS, China’s Hackers Turn Legacy Bugs into Global Espionage Tools
A China-linked threat actor has been attributed to a cyber attack targeting an U.S. non-profit organization with an…
November 7, 2025
Hidden Logic Bombs in Malware-Laced NuGet Packages Set to Detonate Years After Installation
A set of nine malicious NuGet packages has been identified as capable of dropping time-delayed payloads to sabotage…
November 7, 2025
Enterprise Credentials at Risk – Same Old, Same Old?
Imagine this: Sarah from accounting gets what looks like a routine password reset email from your organization’s cloud…
November 7, 2025
Google Launches New Maps Feature to Help Businesses Report Review-Based Extortion Attempts
Google on Thursday said it’s rolling out a dedicated form to allow businesses listed on Google Maps to…
November 7, 2025
Vibe-Coded Malicious VS Code Extension Found with Built-In Ransomware Capabilities
Cybersecurity researchers have flagged a malicious Visual Studio Code (VS Code) extension with basic ransomware capabilities that appears…
November 7, 2025
Trojanized ESET Installers Drop Kalambur Backdoor in Phishing Attacks on Ukraine
A previously unknown threat activity cluster has been observed impersonating Slovak cybersecurity company ESET as part of phishing…
November 6, 2025
From Tabletop to Turnkey: Building Cyber Resilience in Financial Services
Introduction Financial institutions are facing a new reality: cyber-resilience has passed from being a best practice, to an…
November 6, 2025
ThreatsDay Bulletin: AI Tools in Malware, Botnets, GDI Flaws, Election Attacks & More
Cybercrime has stopped being a problem of just the internet — it’s becoming a problem of the real…
November 6, 2025