The Importance of Behavioral Analytics in AI-Enabled Cyber Attacks
Artificial Intelligence (AI) is changing how individuals and organizations conduct many activities, including how cybercriminals carry out phishing…
March 20, 2026
DoJ Disrupts 3 Million-Device IoT Botnets Behind Record 31.4 Tbps Global DDoS Attacks
The U.S. Department of Justice (DoJ) on Thursday announced the disruption of command-and-control (C2) infrastructure used by several…
March 20, 2026
Apple Warns Older iPhones Vulnerable to Coruna, DarkSword Exploit Kit Attacks
Apple is urging users who are still running an outdated version of iOS to update their iPhones to…
March 20, 2026
Speagle Malware Hijacks Cobra DocGuard to Steal Data via Compromised Servers
Cybersecurity researchers have flagged a new malware dubbed Speagle that hijacks the functionality and infrastructure of a legitimate…
March 19, 2026
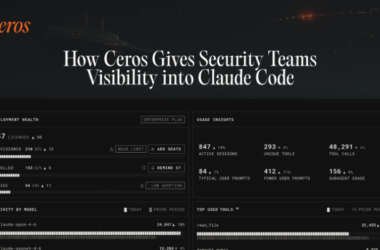
How Ceros Gives Security Teams Visibility and Control in Claude Code
Security teams have spent years building identity and access controls for human users and service accounts. But a…
March 19, 2026
DarkSword iOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for Full Device Takeover
A new exploit kit for Apple iOS devices designed to steal sensitive data from is being wielded by…
March 19, 2026
CISA Warns of Zimbra, SharePoint Flaw Exploits; Cisco Zero-Day Hit in Ransomware Attacks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has urged government agencies to apply patches for two security…
March 19, 2026
OFAC Sanctions DPRK IT Worker Network Funding WMD Programs Through Fake Remote Jobs
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has sanctioned six individuals and two…
March 18, 2026
Interlock Ransomware Exploits Cisco FMC Zero-Day CVE-2026-20131 for Root Access
Amazon Threat Intelligence is warning of an active Interlock ransomware campaign that’s exploiting a recently disclosed critical security…
March 18, 2026
Product Walkthrough: How Mesh CSMA Reveals and Breaks Attack Paths to Crown Jewels
Security teams today are not short on tools or data. They are overwhelmed by both. Yet within the…
March 18, 2026