Android 17 Blocks Non-Accessibility Apps from Accessibility API to Prevent Malware Abuse
Google is testing a new security feature as part of Android Advanced Protection Mode (AAPM) that prevents certain…
March 16, 2026
OpenClaw AI Agent Flaws Could Enable Prompt Injection and Data Exfiltration
China’s National Computer Network Emergency Response Technical Team (CNCERT) has issued a warning about the security stemming from…
March 14, 2026
GlassWorm Supply-Chain Attack Abuses 72 Open VSX Extensions to Target Developers
Cybersecurity researchers have flagged a new iteration of the GlassWorm campaign that they say represents a “significant escalation”…
March 14, 2026
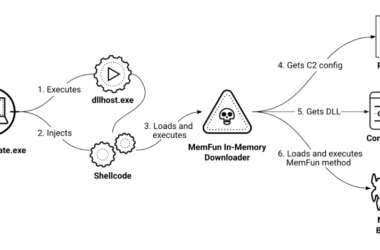
Chinese Hackers Target Southeast Asian Militaries with AppleChris and MemFun Malware
A suspected China-based cyber espionage operation has targeted Southeast Asian military organizations as part of a state-sponsored campaign…
March 13, 2026
Meta to Shut Down Instagram End-to-End Encrypted Chat Support Starting May 2026
Meta has announced plans to discontinue support for end-to-end encryption (E2EE) for chats on Instagram after May 8,…
March 13, 2026
INTERPOL Dismantles 45,000 Malicious IPs, Arrests 94 in Global Cybercrime
INTERPOL on Friday announced the takedown of 45,000 malicious IP addresses and servers used in connection with phishing,…
March 13, 2026
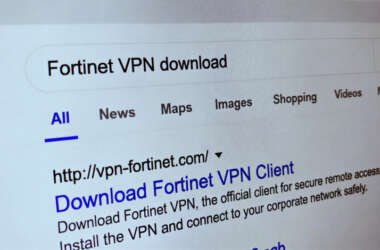
Storm-2561 Spreads Trojan VPN Clients via SEO Poisoning to Steal Credentials
Microsoft has disclosed details of a credential theft campaign that employs fake virtual private network (VPN) clients distributed…
March 13, 2026
Investigating a New Click-Fix Variant
Disclaimer: This report has been prepared by the Threat Research Center to enhance cybersecurity awareness and support the…
March 13, 2026
Google Fixes Two Chrome Zero-Days Exploited in the Wild Affecting Skia and V8
Google on Thursday released security updates for its Chrome web browser to address two high-severity vulnerabilities that it…
March 13, 2026
Nine CrackArmor Flaws in Linux AppArmor Enable Root Escalation, Bypass Container Isolation
Cybersecurity researchers have disclosed multiple security vulnerabilities within the Linux kernel’s AppArmor module that could be exploited by…
March 13, 2026